Software Tools
Disassemblers, Decompilers, Development Tools, Schematic/PCB Capture and other reverse engineering software. If you used it while reverse engineering, list it here!
Contents
- 1 Tool Index
- 1.1 RF Signals Analysis
- 1.2 RF Signals Analysis Operating System
- 1.3 Firmware Analysis
- 1.4 Setup or Overlay Unpackers / Extractors
- 1.5 Binary PE Analysis / Editor (Windows)
- 1.6 Hex Editors
- 1.7 Pattern Matching / Pattern Searching
- 1.8 IAT Reconstructors (Windows)
- 1.9 Process Dumpers (Windows)
- 1.10 API monitoring ring3 (Windows)
- 1.11 Virtualization technology (host isolation) or sandboxes
- 1.12 Debugger / disassembler for unmanged binaries
- 1.13 Debugging and Profiling dynamic analysis (Linux)
- 1.14 Debugger / disassembler for manged binaries
- 1.15 PC platform exploration frameworks
- 1.16 Mobile exploration frameworks
- 1.17 Promiscuous mode eavesdropping TCP/UDP
- 1.18 HTTP(S) Debuggers / Web Debuggers
- 1.19 Other Network Tools
- 1.20 Unified Extensible Firmware Interface (UEFI) & legacy PC BIOS Tools
- 1.21 Operating System for Penetration Testing & Digital Forensics
- 1.22 Privacy Operating System
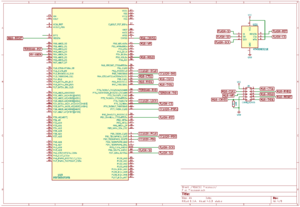
- 1.23 Tools for opening CAD or Boardview files
- 1.24 Electronics Design Automation (EDA) Suite for Developing Custom PCB's
- 1.25 Computer Aided Design (CAD) Mechanical Engineering
- 1.26 Web Browsing
- 1.27 Public Networks
- 1.28 Email Clients / Email Encryption Standards
- 1.29 Chat Applications / Platforms
- 1.30 Disk Encryption Software
- 1.31 Image Manipulation Tools
- 1.32 Video Editing Software / 3D Creation / Dec, Enc, Transcode, etc / Media Players
- 1.33 Video Recording and Live Streaming
- 1.34 Social Network (self-hosted & open-source)
- 2 Education
Tool Index
RF Signals Analysis
- Universal Radio Hacker - tool to analyze and extract data from SDR-captured radio signals (especially pilots, ISM RF devices, etc). See youtube for tutorials and examples.
- GNU Radio - toolkit that provides signal processing blocks to implement software-defined radios and signal processing systems.
- CubicSDR - is a cross-platform Software-Defined Radio application which allows you to navigate the radio spectrum and demodulate any signals you might discover.
- Audacity - is a audio editor that can be used to cleanup the radio waves captured by a SDR or Software Defined Radio. (Example: Start Audacity -> Import –> Raw Data -> Radio Wave File)
RF Signals Analysis Operating System
- DragonOS - Out of the box OS for SDRs. Supports Raspberry Pi and x86-64.
- The list Operating System for Penetration Testing & Digital Forensics will also be sufficient for the SDR playfield.
Firmware Analysis
- binwalk - Binwalk is a fast, easy to use tool for analyzing, reverse engineering, and extracting firmware images.
- FAT - is a toolkit built in order to help security researchers analyze and identify vulnerabilities in IoT and embedded device firmware.
- EMBA - is designed as the central firmware analysis tool for penetration testers and product security teams. It supports the complete security analysis process starting with firmware extraction, doing static analysis and dynamic analysis via emulation and finally generating a web report.
- Firmware Modification Kit - is a collection of scripts and utilities to extract and rebuild linux based firmware images.
- Firmwalker - is a script for searching the extracted firmware file system for goodies!
Setup or Overlay Unpackers / Extractors
- innounp - the Inno Setup Unpacker.
- Universal Extractor 2 (UniExtract2) - is a tool designed to extract files from any type of extractable file.
- lessmsi - a tool to view and extract the contents of an Windows Installer (.msi) file.
- FUU - [F]aster [U]niversal [U]npacker.
Binary PE Analysis / Editor (Windows)
- ProtectionID - Great little tool to scan a Windows binary payload for overlays and packers. File:ProtectionId.690.December.2017.zip VT link, pw: recessim.com
- Detect-It-Easy - abbreviated "DIE" is a program for determining types of files. "DIE" is a cross-platform application, apart from Windows version there are also available versions for Linux and Mac OS.
- MiTeC Portable Executable Reader/Explorer - is a tool that reads and displays executable file properties and structures. It is compatible with PE32 (Portable Executable), PE32+ (64bit), NE (Windows 3.x New Executable) and VxD (Windows 9x Virtual Device Driver) file types. .NET executables are supported too.
- ExeInfoPe - is a tool that can detect packers, compilers, protectors, .NET obfuscators, PUA applications.
- PE-bear - is a Portable Executable reversing tool with a friendly GUI using the Capstone Engine and is Open Source!
- CFF Explorer - is a PE editor called CFF Explorer and a process viewer with a lot of features.
- RDG Packer Detector - is a detector for packers, cryptors, compilers, installers.
Hex Editors
- ImHex - is a Hex Editor for Reverse Engineers, Programmers and people who value their retinas when working at 3 AM.
- HxD - is a carefully designed and fast hex editor which, additionally to raw disk editing and modifying of main memory (RAM), handles files of any size.
- WinHex - is in its core a universal hexadecimal editor, particularly helpful in the realm of computer forensics, data recovery, low-level data processing, and IT security.
- MalCat - is a feature-rich hexadecimal editor / disassembler for Windows and Linux targeted to IT-security professionals. Inspect more than 40 binary file formats, dissassemble and decompile different CPU architectures, extract embedded files and scan for Yara signatures or anomalies in a fast and easy-to-use graphical interface.
Pattern Matching / Pattern Searching
- Yara - is a pattern matching swiss knife in the IT Security Researchers branch.
- ripgrep (rg) - is a line-oriented search tool that recursively searches the current directory for a regex pattern. By default, ripgrep will respect gitignore rules and automatically skip hidden files/directories and binary files.
- grep - searches the named input FILEs (or standard input if no files are named, or if a single hyphen-minus (-) is given as file name) for lines containing a match to the given PATTERN. By default, grep prints the matching lines.
- grepWin - is a simple yet powerful search and replace tool which can use regular expressions to do its job. This allows to do much more powerful searches and replaces.
- AstroGrep - is a Microsoft Windows grep utility. Grep is a UNIX command-line program which searches within files for keywords. AstroGrep supports regular expressions, versatile printing options, stores most recently used paths and has a "context" feature which is very nice for looking at source code.
IAT Reconstructors (Windows)
- NtQuery Scylla - is a Windows Portable Executable imports reconstructor Open Source and part of x64dbg.
Process Dumpers (Windows)
- Process Dump (pd) - is a Windows reverse-engineering tool to dump malware memory components back to disk for analysis. It uses an aggressive import reconstruction approach to make analysis easier, and supports 32 and 64 bit modules. Dumping of regions without PE headers is supported and in these cases PE headers and import tables will automatically be generated.
- KsDumper - is a tool for dumping processes using the power of kernel space.
API monitoring ring3 (Windows)
- WinAPIOverride - is an advanced api monitoring software for 32 and 64 bits processes. You can monitor and/or override any function of a process.
- Rohitab API Monitor - is a free software that lets you monitor and control API calls made by applications and services. Its a powerful tool for seeing how applications and services work or for tracking down problems that you have in your own applications.
- tiny_tracer - is a Pin Tool for tracing API calls including parameters of selected functions, selected instructions RDTSC, CPUID, INT, inline system calls inc parameters of selected syscalls and more.
Virtualization technology (host isolation) or sandboxes
- Firecracker - is an open source virtualization technology that is purpose-built for creating and managing secure, multi-tenant container and function-based services that provide serverless operational models.
- Red Hat OpenShift Virtualization - Red Hat® OpenShift® Virtualization, a feature of Red Hat OpenShift, allows IT teams to run virtual machines alongside containers on the same platform, simplifying management and improving time to production.
- Xen Project - The Xen Project focuses on revolutionizing virtualization by providing a versatile and powerful hypervisor that addresses the evolving needs of diverse industries.
- Sandboxie - is a sandbox-based isolation software for 32-bit and 64-bit Windows NT-based operating systems. It creates a sandbox-like isolated operating environment in which applications can be run or installed without permanently modifying local & mapped drives or the Windows registry.
- boxxy-rs - is a linkable sandbox explorer. "If you implement boundaries and nobody is around to push them, do they even exist?". Have you ever wondered how your sandbox looks like from the inside? Tempted to test if you can escape it, if only you had a shell to give it a try?
- Oracle VM VirtualBox - is a powerful x86 and AMD64/Intel64 virtualization product for enterprise as well as home use. Not only is VirtualBox an extremely feature rich, high performance product for enterprise customers, it is also the only professional solution that is freely available as Open Source Software under the terms of the GNU General Public License (GPL) version 3.
- VMware - is a virtualization and cloud computing software provider based in Palo Alto, Calif.
- QEMU - A generic and open source machine emulator and virtualizer.
- KVM (for Kernel-based Virtual Machine) - is a full virtualization solution for Linux on x86 hardware containing virtualization extensions (Intel VT or AMD-V). It consists of a loadable kernel module, kvm.ko, that provides the core virtualization infrastructure and a processor specific module, kvm-intel.ko or kvm-amd.ko.
- Proxmox - is a complete, open-source server management platform for enterprise virtualization. It tightly integrates the KVM hypervisor and Linux Containers (LXC), software-defined storage and networking functionality, on a single platform.
Debugger / disassembler for unmanged binaries
- Binary Ninja - reverse-engineering platform that can disassemble a binary and display the disassembly in linear or graph views.
- Ghidra - Ghidra is an open source software reverse engineering (SRE) framework developed by NSA's Research Directorate for NSA's cybersecurity mission.
- Ghidra Scripts/Plugins/Extension
- Scripts/Plugins/Extension - A curated list of awesome Ghidra materials.
- Ghidra Scripts/Plugins/Extension
- IDA - The IDA Disassembler and Debugger is an interactive, programmable, extensible, multi-processor disassembler hosted on Windows, Linux, or Mac OS X.
- IDA Scripts/Plugins/Extension
- IDA ARM - This script will give you the list of ARM system instructions used in your IDA database. This is useful for locating specific low-level pieces of code (setting up the MMU, caches, fault handlers, etc.).
- BinDiff - is a Open Source comparison tool for binary files, that assists vulnerability researchers and engineers to quickly find differences and similarities in disassembled code.
- Keypatch - A multi-architeture assembler for IDA. Keypatch allows you enter assembly instructions to directly patch the binary under analysis. Powered by Keystone engine.
- IDAStealth - is a plugin which aims to hide the IDA debugger from most common anti-debugging techniques. The plugin is composed of two files, the plugin itself and a dll which is injected into the debugger as soon as the debugger attaches to the process.
- ida-sploiter - is a exploit development and vulnerability research tool. Some of the plugin's features include a powerful ROP gadgets search engine, semantic gadget analysis and filtering, interactive ROP chain builder, stack pivot analysis, writable function pointer search, cyclic memory pattern generation and offset analysis, detection of bad characters and memory holes, and many others.
- IDAtropy -is a plugin for Hex-Ray's IDA Pro designed to generate charts of entropy and histograms using the power of idapython and matplotlib
- Localxrefs - Finds references to any selected text from within the current function.
- Labeless - is a plugin system for dynamic, seamless and realtime synchronization between IDA Database and Olly. Labels, function names and global variables synchronization is supported. Olly and x64dbg are supported.
- Turbodiff - is a binary diffing tool developed as an IDA plugin. It discovers and analyzes differences between the functions of two binaries.
- A list of IDA Plugins (click here for more) - A large list/collection of plugins for IDA.
- IDA Scripts/Plugins/Extension
- Vivisect - Vivisect binary analysis framework. Includes Disassembler, Debugger, Emulation and Symbolik analysis engines. Includes built-in Server and Shared-Workspace functionality. Runs interactive or headless, programmable, extensible, multi-processor disassembler hosted on Windows, Linux, or Mac OS X (Pure-Python, using ctypes to access underlying OS debug mechanism). Supports RevSync via plugin, allowing basic collaboration with Binja, Ghidra, and IDA. Criticisms (from a core dev): "Graph View could use some work, slower than Binja and IDA (due to Python), documentation like an OpenSource Project... but we keep working to make it better. PR's and suggestions welcome." Best installed via Pip:
python3 -m pip install vivisect
- Veles - Open source tool for binary data analysis (No longer actively developed).
- Immunity Debugger - is a powerful new way to write exploits, analyze malware, and reverse engineer Windows binary files (python support)
- Hopper - Hopper can use LLDB or GDB, which lets you debug and analyze the binary in a dynamic way (only for Mac and Linux hosts, not for mobile devices).
- x64dbg - Is a powerful Open Source Ollydbg replacement with a User Interface very similar to Ollydbg also x64dbg as the name states offers x64 support.
- x64dbg Plugins/Integrations/Templates
- x64dbg's Wiki - is a wiki of Integrations and Plugins of x64dbg debugger.
- x64dbg Plugins/Integrations/Templates
- Reko - Reko is a binary decompiler for static analysis (ARM, x86-64, M68K, Aarch65, RISC-V and dotnet)
- radare2 and Rizin - radare2 and its fork Rizin are open source reverse engineering frameworks. Both are primarily used through a shell-like text UI, but also offer GUIs called iaito and Cutter respectively.
- Cutter - is a free and open-source reverse engineering platform powered by rizin. It aims at being an advanced and customizable reverse engineering platform while keeping the user experience in mind. Cutter is created by reverse engineers for reverse engineers.
- Plasma - Plasma is an interactive disassembler for x86/ARM/MIPS. It can generates indented pseudo-code with colored syntax.
- edb - is a cross platform AArch32/x86/x86-64 debugger. It was inspired by Ollydbg, but aims to function on AArch32, x86, and x86-64 as well as multiple OS's.
- Medusa - is a disassembler designed to be both modular and interactive. It runs on Windows and Linux, it should be the same on OSX.
- rVMI - is a debugger on steroids. It leverages Virtual Machine Introspection (VMI) and memory forensics to provide full system analysis. This means that an analyst can inspect userspace processes, kernel drivers, and pre-boot environments in a single tool.
- GDB - the GNU Project debugger, allows you to see what is going on `inside' another program while it executes, or what another program was doing at the moment it crashed.
- GDB Plugins/Integrations/Templates
- pwndbg - is a GDB plug-in that makes debugging with GDB suck less, with a focus on features needed by low-level software developers, hardware hackers, reverse-engineers and exploit developers.
- GDB Plugins/Integrations/Templates
- Capstone - is a disassembly/disassembler framework for ARM, ARM64 (ARMv8), BPF, Ethereum VM, M68K, M680X, Mips, MOS65XX, PPC, RISC-V(rv32G/rv64G), SH, Sparc, SystemZ, TMS320C64X, TriCore, Webassembly, XCore and X86.
Debugging and Profiling dynamic analysis (Linux)
- valgrind - Valgrind is a GPL'd system for debugging and profiling Linux programs. With Valgrind's tool suite you can automatically detect many memory management and threading bugs, avoiding hours of frustrating bug-hunting, making your programs more stable.
- jTracer - is a stack trace visualization utility for libcsdbg. In other words, it acts as a TCP/IP server for libcsdbg clients, that connect to it and transfer their trace data, either C++ exception stack traces or generic thread stack traces and whole process stack dumps.
Debugger / disassembler for manged binaries
.NET (CLR)
- dnSpyEx (newly maintained repo & added features) - is a debugger and .NET assembly editor. You can use it to edit and debug assemblies even if you don't have any source code available.
- dnSpy (archived repo) - is a debugger and .NET assembly editor. You can use it to edit and debug assemblies even if you don't have any source code available.
- Iced - Blazing fast and correct x86/x64 disassembler, assembler, decoder, encoder for Rust, .NET, Java, Python, Lua.
- ILSpy - NET Decompiler with support for PDB generation, ReadyToRun, Metadata (&more) - cross-platform!
- Telerik JustDecompile - is a free .NET decompiler and assembly browser that makes high-quality .NET decompilation easy With an open source decompilation engine.
.NET deobfuscators
- de4dot CEx - is a deobfuscator based on de4dot with full support for vanilla ConfuserEx.
- de4dot - is a .NET deobfuscator and unpacker.
- Lists of .NET deobfuscators and unpackers (Open Source) - A curated list of open source deobfuscators and more.
.NET memory dumpers
- ExtremeDumper - is a .NET Assembly Dumper (source code available).
- MemoScope.Net - is a tool to analyze .Net process memory: it can dump an application's memory in a file and read it later. The dump file contains all data (objects) and threads (state, stack, call stack).
- ClrDumper - is a tool that can dump .NET assemblies and scripts from native clr loaders, managed assembly and vbs, jscript or powershell scripts.
.NET tracers
- dotNET Tracer 2.0 by Kurapika - is a simple tool that has a similar functionality to RegMon or FileMon but it's designed to trace events in .NET assemblies in runtime. File:KDT2.0.zip VT1 VT2 (thermida packed), pw: recessim.com
- TraceSpy - is a open source and free, alternative to the very popular SysInternals DebugView tool.
JAVA (JVM)
- Recaf - Recaf is an open-source Java bytecode editor that simplifies the process of editing compiled Java applications.
- JEB decompiler - Decompile and debug Android dalvik, Intel x86, ARM, MIPS, RISC-V, S7 PLC, Java, WebAssembly & Ethereum Decompilers.
JAVA (ART/APK)
- Jadx - Dex to Java decompiler. Command-line and GUI tools for producing Java source code from Android Dex and apk files.
- APKinspector - is a powerful GUI tool for analysts to analyze the Android applications.
- Apktool - A tool for reverse engineering Android apk files.
- Bytecode viewer - is a Java 8+ Jar & Android APK Reverse Engineering Suite (Decompiler, Editor, Debugger & More)
- ShowJava - is an APK (android application), JAR & Dex decompiler for android.
- TTDeDroid - is a tool for quickly decompiling apk/aar/dex/jar.
- smali/baksmali - is an assembler/disassembler for the dex format used by dalvik, Android's Java VM implementation. The syntax is loosely based on Jasmin's/dedexer's syntax.
JAVA deobfuscators (mixed platforms)
- deobfuscator - is a project that aims to deobfuscate most commercially-available obfuscators for Java. GUI version github
- Threadtear - is a multifunctional deobfuscation tool for java, ZKM and Stringer support, Android support is in development.
- Another Deobfuscator - Some deobfuscator for java. Supports superblaubeere27 / JObf / sb27, Paramorphism 2.1.2_9, Caesium, Monsey, Skid/qProtect, Scuti, CheatBreaker, Bozar, ...
PYTHON
- uncompyle6 - is a native Python cross-version decompiler and fragment decompiler. The successor to decompyle, uncompyle, and uncompyle2.
- pycdc - is a C++ python bytecode disassembler and decompiler.
- PyREBox - is a Python scriptable Reverse Engineering sandbox by Cisco-Talos. It is based on QEMU, and its goal is to aid reverse engineering by providing dynamic analysis and debugging capabilities from a different perspective.
- Voltron - is an extensible debugger UI toolkit written in Python. It aims to improve the user experience of various debuggers (LLDB, GDB, VDB and WinDbg) by enabling the attachment of utility views that can retrieve and display data from the debugger host.
PC platform exploration frameworks
- Chipsec - is a framework for analyzing the security of PC platforms including hardware, system firmware (BIOS/UEFI), and platform components. It includes a security test suite, tools for accessing various low level interfaces, and forensic capabilities.
- Metasploit Framework - is a Ruby-based Framework, modular penetration testing platform that enables you to write, test, and execute exploit code.
- Arachni - is a feature-full, modular, high-performance Ruby framework aimed towards helping penetration testers and administrators evaluate the security of web applications.
- Burp Suite - Burp or Burp Suite is a set of tools used for penetration testing of web applications.
Mobile exploration frameworks
- Frida - Dynamic instrumentation toolkit for developers, reverse-engineers, and security researchers.
- objection - is a runtime mobile exploration toolkit, powered by Frida, built to help you assess the security posture of your mobile applications, without needing a jailbreak.
- AppAudit - is an efficient program analysis tool that detects data leaks in mobile applications. It can accurately find all leaks within seconds and ~200 MB memory.
- LSPlant - is an Android ART hook library, providing Java method hook/unhook and inline deoptimization.
- LSposed - is a Riru / Zygisk module trying to provide an ART hooking framework which delivers consistent APIs with the OG Xposed, leveraging LSPlant hooking framework.
- LSPosed Module Repository
- Xposed Modules Repo - New Xposed(LSPosed) Module Repository.
- LSPosed Module Repository
- Xposed Framework - is a framework for mobile exploration hooking and modifying code on the fly. Inline API hooking example.
- Xposed modules
- JustTrustMe - Art framework hook to patch okHTTP and other common libs to fool the CERT chain in order for Mitmproxy to capture TLS traffic in cleartext.
- FakeXposed - Hide xposed, root, file redirection, two-way shielding data detection.
- SSLUnpinning_Xposed - Android Xposed Module to bypass SSL certificate validation (Certificate Pinning)..
- Xposed modules
- Xposed Framework API Development Documentation
- Xposed API Reference - Javadoc reference of the Xposed Framework API. It's meant for module developers who want to understand which classes and methods they can use.
- Xposed Framework API Development Documentation
Promiscuous mode eavesdropping TCP/UDP
- Mitmproxy - is an interactive TLS-capable intercepting HTTP proxy for penetration testers and software developers.
- Wireshark - is a network traffic analyzer, or "sniffer", for Linux, macOS, *BSD and other Unix and Unix-like operating systems and for Windows.
- Zed Attack Proxy (ZAP) - is an Open Source & easy to use integrated penetration testing tool for finding vulnerabilities in web applications.
- Mallet - is an intercepting proxy for arbitrary protocols.
- PETEP (PEnetration TEsting Proxy) - is an open-source Java application for traffic analysis & modification using TCP/UDP proxies. PETEP is a useful tool for performing penetration tests of applications with various application protocols.
HTTP(S) Debuggers / Web Debuggers
- HTTP Toolkit - is a beautiful, cross-platform & open-source HTTP(S) debugging proxy, analyzer & client, with built-in support for modern tools from Docker to Android to GraphQL.
- httpry - is a HTTP logging and information retrieval tool written in Perl and C.
- Requestly - Bring the power of Charles Proxy, Fiddler & Postman together with beautiful, modern UI & collaboration features.
- Fiddler - is a Web Debugger is a serviceable web debugging proxy for logging all HTTP(S) traffic linking your computer and the internet, allowing for traffic inspection, breakpoint setting, and more.
Other Network Tools
- tcpview - is a tool that will enumerate all active TCP and UDP endpoints, resolving all IP addresses to their domain name versions (Windows).
- cports - is network monitoring software that displays the list of all currently opened TCP/IP and UDP ports on your local Windows computer.
- NetworkMiner - is an open source network forensics tool that extracts artifacts, such as files, images, emails and passwords, from captured network traffic in PCAP files.
- netstat - is a Linux CLI tool to print network connections, routing tables, interface statistics, masquerade connections, and multicast memberships.
Unified Extensible Firmware Interface (UEFI) & legacy PC BIOS Tools
- UEFI
- UEFITool / UEFIExtract / UEFIFind - is a UEFI firmware image viewer and editor.
- IFRExtractor-RS - is a Rust utility to extract UEFI IFR (Internal Form Representation) data found in a binary file into human-readable text.
- uefi-firmware-parser - is a cross-platform open source application written in Python. Very tinker-friendly. Can be used in scripts to automate firmware patching.
- AMIBCP_5.01_x64 - AMI BIOS Configuration Program (AMIBCP) is a powerful customization utility that enables OEMs/ODMs to customize the Aptio® ROM image without intervening on the source code. VT link
- AMIBCP 5.01.0014 x64 VT link
- AMIBCP_5.02.0023 VT link
- AMIBCP_5.02.0031 VT link
- AMIBCP 5.02.0034 VT link
- UEFI
- BIOS
- PhoenixTool - is a Windows-only freeware GUI application written in C#. Used mostly for SLIC-related modifications, but it not limited to this task. Requires Microsoft .NET 3.5 to work properly. Supports unpacking firmware images from various vendor-specific formats like encrypted HP update files and Dell installers.
- AMI
- AMIBCP_2.25 VT link
- AMIBCP_2.43 VT link
- AMIBCP_3.13 VT link
- AMIBCP_3.37 VT link
- AMIBCP_3.46 VT link
- AMIBCP_3.47 VT link
- AMIBCP_3.51 VT link
- AMIBCP_4.53 VT link
- AMIBCP_4.55 VT link
- MMTOOL_2.22.1 - MMtool stands for Module Management Tool. As one of AMI's BIOS/UEFI utilities, MMTool allows users to manage firmware file modules within the Aptio ROM image. VT link
- MMTOOL_3.12 VT link
- MMTOOl_3.19 VT link
- MMTOOL_3.19_Mod_21FiX VT link
- MMTOOL_3.22 VT link
- MMTOOL_3.22_1B_21Fix-BKMOD VT link
- MMTOOL_3.22_CN_BKMod VT link
- MMTOOL_3.23_CN_BKMod VT link
- MMTOOL_3.26 VT link
- MMTOOL_4.50.0.23VT link
- MMTOOL_5.0.07 VT link
- MMTOOL_5.02.0024 VT link
- MMTOOL_5.02.0025 VT link
- Award
- Award Bios Editor - is a editor for Award bios.
- Insyde
- H2OEZE_x86_WIN_100.00.02.13 - H2OEZE™: Easy BIOS Editor that helps edit binaries in the BIOS, including Option ROMs, driver binaries, logos, and Setup values. VT link
- H2OEZE_x86_WIN_100.00.03.04 VT link
- H2OEZE_x64_WIN_100.00.03.04 VT link
- BIOS
- Download all* tools in one archive, click here. VT link
- Bios password resetting
- HP BIOS Password Reset by MAZZIF - A live USB tool made by Mazzif to reset older HP BIOS passwords. VT link
Operating System for Penetration Testing & Digital Forensics
- Kali Linux - is an open-source, Debian-based Linux distribution geared towards various information security tasks, such as Penetration Testing, Security Research, Computer Forensics and Reverse Engineering.
- BlackBox is more than an operating system, it is a Free Open Source Community Project with the aim of promoting the culture of security in IT environment and give its contribution to make it better and safer.
- BlackArch - is an Arch Linux-based penetration testing distribution for penetration testers and security researchers.
- Parrot Security - is based on top of Debian, the most advanced and recognized universal operating system that can run anywhere.
- Fedora Security Spin - is a live media based on Fedora to provide a safe test environment for working on security auditing, forensics and penetration testing, coupled with all the Fedora Security features and tools.
- CAINE - CAINE (Computer Aided INvestigative Environment) is an Italian GNU/Linux live distribution created as a Digital Forensics project.
- Dracos Linux - is the Linux operating system from Indonesia, open source is built based on Debian live project under the protection of the GNU General Public License v3.0. This operating system is one variant of Linux distributions, which is used to perform security testing (penetration testing). Dracos linux in Arm by hundreds hydraulic pentest, forensics and reverse engineering.
- Pentoo - is a Live CD and Live USB designed for penetration testing and security assessment. Based off Gentoo Linux, Pentoo is provided both as 32 and 64 bit installable livecd.
Privacy Operating System
- Tails - is a portable operating system that protects against surveillance and censorship.
Tools for opening CAD or Boardview files
Description: Boardview is a type of file containing information about printed circuit boards, their components, used signals, test points and more. These files may have following extensions: .asc, .bdv, .brd, .bv, .cad, .cst, .gr, .f2b, .fz, .tvw and others.
- FlexBV - Advanced FlexBV boardview software integrates your boardview files with PDF schematics to substantially ease the process of tracking down faults and understanding damaged boards
- OpenBoardView - is a Open Source Linux SDL/ImGui edition software for viewing .brd files, intended as a drop-in replacement for the "Test_Link" software and "Landrex".
- Allegro®/OrCAD® FREE Physical Viewer - is a free download that allows you to view and plot databases from Allegro PCB Editor, OrCAD PCB Editor, Allegro Package Designer, and Allegro PCB SI technology.
- BoardViewer - is software intended for viewing various boardview file types like .tvw files and much more supported formats.
- CADview - simple old tool for viewing CAD files of PCB's (Windows). File:CAD View.zip VT link
For resources to open in your favorite boardview program visit Literature -> 1.2 Datasheets boardviews & schematics
Electronics Design Automation (EDA) Suite for Developing Custom PCB's
- KiCad - is a free software suite for electronic design automation (EDA). It facilitates the design and simulation of electronic hardware. It features an integrated environment for schematic capture, PCB layout, manufacturing file viewing, ngspice-provided SPICE simulation, and engineering calculation.
- EasyEDA - EasyEDA is a web-based EDA tool suite that enables hardware engineers to design, simulate, share - publicly and privately - and discuss schematics, simulations and printed circuit boards. It can also be used offline.
- Fritzing - is an open-source hardware initiative that makes electronics accessible as a creative material for anyone.
- LibrePCB - is a free, cross-platform, easy-to-use electronic design automation suite to draw schematics and design printed circuit boards – for makers, students and professionals, from beginners to experts.
- gEDA Project - The gEDA project has produced and continues working on a full GPL'd suite and toolkit of Electronic Design Automation tools. These tools are used for electrical circuit design, schematic capture, simulation, prototyping, and production.
- pcb-rnd - is a free/open source, flexible, modular Printed Circuit Board editor. For design of professional and hobby boards. Is feature-rich and compatible. Has a long history, fast paced development, and big plansand is part of the coralEDA ecosystem.
Computer Aided Design (CAD) Mechanical Engineering
- FreeCAD - is an open-source parametric 3D modeler made primarily to design real-life objects of any size. Parametric modeling allows you to easily modify your design by going back into your model history and changing its parameters.
- OpenSCAD - is software for creating solid 3D CAD objects. It is free software and available for Linux/UNIX, MS Windows and Mac OS X.
- BRL-CAD - is a powerful open source cross-platform solid modeling system that includes interactive geometry editing, high-performance ray-tracing for rendering and geometric analysis, a system performance analysis benchmark suite, geometry libraries for application developers, and more than 30 years of active development.
- SolveSpace - is a free (GPLv3) parametric 3d CAD tool. Modeling 3d parts, modeling 2d parts, 3d-printed parts, preparing CAM data, mechanism design, plane and solid geometry.
Web Browsing
- Mozilla Firefox - is a free, open source web browser developed by the Mozilla Foundation and Mozilla Corporation in 2004. The Firefox web browser can be used with Windows, Mac and Linux operating systems, as well as Android and iOS mobile devices.
- Extensions & Configurations
- NoScript - The popular NoScript Security Suite browser extension.
- WebRTC block - WebRTC leaks your actual IP addresses from behind your VPN, by default. With this extension you can disable it.
- user.js - Firefox privacy, security and anti-tracking: a comprehensive user.js template for configuration and hardening.
- Betterfox - Firefox speed, privacy, and security: a user.js template for configuration. Your favorite browser, but better.
- Extensions & Configurations
- Tor Browser - Tor (The Onion Router) is a network that anonymizes web traffic to provide truly private web browsing. The Tor Browser hides your IP address and browsing activity by redirecting web traffic through a series of different routers known as nodes.
- Orbot for Android - is a free proxy app that empowers other apps to use the internet more securely. Orbot uses Tor to encrypt your Internet traffic and then hides it by bouncing through a series of computers around the world. Tor is free software and an open network that helps you defend against a form of network surveillance that threatens personal freedom and privacy, confidential business activities.
Public Networks
- Tor - is an open-source privacy network that enables anonymous web browsing. The worldwide Tor computer network uses secure, encrypted protocols to ensure that users' online privacy is protected.
- The Invisible Internet Project (I2P) - is a fully encrypted private network layer. It protects your activity and location. Every day people use the network to connect with people without worry of being tracked or their data being collected.
- FreeNet - is a peer-to-peer platform for censorship-resistant, anonymous communication. It uses a decentralized distributed data store to keep and deliver information, and has a suite of free software for publishing and communicating on the Web without fear of censorship.
- ZeroNet - Open, free and uncensorable websites, using Bitcoin cryptography and BitTorrent network · We believe in open, free, and uncensored network.
- Lokinet - is an onion-router that lets you access the internet anonymously. Built on LLARP, the fastest onion-routing protocol in the world.
- Nym - protect internet traffic by routing it through a decentralised mixnet that can be accessed anonymously using zk-nyms.
Email Clients / Email Encryption Standards
- Mozilla ThunderBird - is a free, open-source, cross-platform application for managing email, news feeds, chat, and news groups. It is a local email application, meaning it installs and runs as a client on your device, being rather than browser or web-based. FAQ How to implement OpenPGP in Thunderbird.
- OpenPGP - is the most widely used email encryption standard. It is defined by the OpenPGP Working Group of the Internet Engineering Task Force (IETF) as a Proposed Standard in RFC 4880. OpenPGP was originally derived from the PGP software, created by Phil Zimmermann.
- GnuPG - is a complete and free implementation of the OpenPGP standard as defined by RFC4880 (also known as PGP). GnuPG allows you to encrypt and sign your data and communications; it features a versatile key management system, along with access modules for all kinds of public key directories. GnuPG, also known as GPG, is a command line tool with features for easy integration with other applications.
- Evolution - is a personal information management application that provides integrated mail, calendaring and address book functionality. Check the Privacy Policy sub-page for a general information about user data usage. FAQ How to implement OpenPGP in Evolution.
- NeoMutt - is a command line mail reader (or MUA ). It's a fork of Mutt with added features.
Chat Applications / Platforms
- Jabber - is a original messaging service based on XMPP and has been continuously offered for free since 1999.
- XMPP clients
- XMPP client list - is a list of XMPP clients composed by XMPP itself.
- Off-the-Record Messaging (OTR) for XMPP - is a cryptographic protocol that provides encryption for instant messaging conversations. OTR uses a combination of AES symmetric-key algorithm with 128 bits key length, the Diffie–Hellman key exchange with 1536 bits group size, and the SHA-1 hash function.
- XMPP clients
- Session - Session is an end-to-end encrypted messenger that minimises sensitive metadata, designed and built for people who want absolute privacy and freedom from any form of surveillance.
- Briar - is a messaging app designed for activists, journalists, and anyone else who needs a safe, easy and robust way to communicate. Unlike traditional messaging apps, Briar doesn't rely on a central server - messages are synchronized directly between the users' devices.
- Matrix - is an open network for secure, decentralised communication.
- Discord - is a voice, video and text communication service used by over a hundred million people to hang out and talk with their friends and communities.
- Discord client advice
- 1. Stop using the installed electron PC based version. Use the web version.
- 2. Android stock client is spoiled with rubbish code slowing down your SoC and sending loads of analytics, use Aliucord instead (but carefully read the readme.md, ToS issue).
- Discord client advice
Disk Encryption Software
- Linux Unified Key Setup (LUKS) - The Linux Unified Key Setup (LUKS) is a disk encryption specification created by Clemens Fruhwirth in 2004 and originally intended for Linux. LUKS implements a platform-independent standard on-disk format for use in various tools
- VaraCrypt - VeraCrypt is free open-source disk encryption software for Windows, Mac OS X and Linux. Support for on-the-fly encryption (OTFE).
Image Manipulation Tools
- Gimp - is the official website of the GNU Image Manipulation Program (GIMP). GIMP is a cross-platform image editor available for GNU/Linux, macOS, Windows and more operating systems. It is free software, you can change its source code and distribute your changes.
- Paint.net - is image and photo editing software for PCs that run Windows. It features an intuitive and innovative user interface with support for layers, unlimited undo, special effects, and a wide variety of useful and powerful tools. An active and growing online community provides friendly help, tutorials, and plugins.
Video Editing Software / 3D Creation / Dec, Enc, Transcode, etc / Media Players
- DaVinci Resolve - is the world’s only solution that combines editing, color correction, visual effects, motion graphics and audio post production all in one software tool! Its elegant, modern interface is fast to learn and easy for new users, yet powerful for professionals.
- Shotcut - is a free, Open Source, cross-platform video editor for Windows, Mac and Linux. Major features include support for a wide range of formats; no import required meaning native timeline editing; Blackmagic Design support for input and preview monitoring; and resolution support to 4k.
- OpenShot - is a free, Open Source video editor for Linux, Mac, and Windows. We designed OpenShot to be an easy to use, quick to learn, and surprisingly powerful video editor. Easily cut, slice, and edit any video or film.
- Blender - is the free and open source 3D creation suite. It supports the entirety of the 3D pipeline—modeling, rigging, animation, simulation, rendering, compositing and motion tracking, even video editing and game creation.
- FFMPEG (Command line interface to convert different formats) - FFmpeg is the leading multimedia framework, able to decode, encode, transcode, mux, demux, stream, filter and play pretty much anything that humans and machines have created. It supports the most obscure ancient formats up to the cutting edge.
- HandBrake - is an Open Source video transcoder available for Linux, Mac, and Windows. Everyone can use HandBrake to make videos for free. HandBrake is a post-production tool. Its primary purpose is to convert videos from supported source formats to MP4 or MKV format.
- VLC Player - VLC Media Player (also known as VLC) is a free, open source multimedia player developed by VideoLAN Organization. It is one of the oldest (released for the first time in February 2001) free, portable, cross-platform multimedia player. You can use it to play all popular multimedia files and also DVDs, CDs, VCDs and other streaming protocols.
Video Recording and Live Streaming
- OBS (Open Broadcaster Software) - is free and Open Source software for video recording and live streaming.
- StreamLabs - is free live streaming and recording software for Twitch, YouTube, and more for Windows or Mac.
Social Network (self-hosted & open-source)
- Mastodon - is a free and open-source software for running self-hosted social networking services. It has microblogging features similar to Twitter, which are offered by a large number of independently run nodes, known as instances or servers, each with its own code of conduct, terms of service, privacy policy, privacy options, and content moderation policies. Github repo.
Education
Tools are great, and sometimes free! Without knowing how to use them, they can be a big waste of time. Better to spend your time learning the basics, then apply your knowledge.
Reverse Engineering Tutorial - A comprehensive reverse engineering tutorial covering x86, x64, 32-bit ARM & 64-bit ARM architectures.
File:Reverse Engineering Malware IDA & Olly Basics 5 parts by otw v1.pdf - A Reverse Engineering Malware introduction and bare basics IDA & Olly x86 (5 parts) by otw.
Using IDAPython to Make Your Life Easier: Part 1 - As a malware reverse engineer, I often find myself using IDA Pro in my day-to-day activities. It should come as no surprise, seeing as IDA Pro is the industry standard (although alternatives such as radare2 and Hopper are gaining traction). One of the more powerful features of IDA that I implore all reverse engineers to make use of is the Python addition, aptly named ‘IDAPython’, which exposes a large number of IDA API calls.
Some publicly available Malware analysis and Reverse engineering - is a curated list of awesome materials from the user Dump-GUY a former Forensic, Malware Analyst, Reverse Engineer. Youtube channel.
BasicMalwareRE - this room aims towards helping everyone learn about the basics of "Malware Reverse Engineering".
Basic Reverse Engineering with Immunity Debugger - SANS Institute Information Security Reading Room. Basic Reverse Engineering x86 with Immunity Debugger.
Reversing / Malware Analysis / Assembly -resources - is a large list of reversing materials and courses.
Malware and Reverse Engineering Complete Collection - Awesome Malware and Reverse Engineering collection by Joas.