Software Tools
Disassemblers, Decompilers, Development Tools, Schematic/PCB Capture and other reverse engineering software. If you used it while reverse engineering, list it here!
Contents
- 1 Tool Index
- 1.1 RF Signals Analysis
- 1.2 Firmware Analysis
- 1.3 Setup or Overlay Unpackers / Extractors
- 1.4 Binary PE Analysis / Editor (Windows)
- 1.5 Pattern Matching
- 1.6 IAT Reconstructors (Windows)
- 1.7 API monitoring ring3 (Windows)
- 1.8 Debugger / disassembler for unmanged binaries
- 1.9 Debugging and Profiling dynamic analysis (Linux)
- 1.10 Debugger / disassembler for manged binaries
- 1.11 PC platform exploration frameworks
- 1.12 Mobile exploration frameworks
- 1.13 Promiscuous mode eavesdropping TCP/UDP
- 1.14 HTTP(S) Debuggers / Web Debuggers
- 1.15 Other Network Tools
- 1.16 Unified Extensible Firmware Interface (UEFI) & legacy PC BIOS Tools
- 1.17 Operating System for Penetration Testing & Digital Forensics
- 1.18 Privacy Operating System
- 1.19 Tools for opening CAD or Boardview files
- 2 Education
Tool Index
RF Signals Analysis
- Universal Radio Hacker - tool to analyze and extract data from SDR-captured radio signals (especially pilots, ISM RF devices, etc). See youtube for tutorials and examples.
- GNU Radio - toolkit that provides signal processing blocks to implement software-defined radios and signal processing systems.
- Audacity - is a audio editor that can be used to cleanup the radio waves captured by a SDR or Software Defined Radio. (Example: Start Audacity -> Import –> Raw Data -> Radio Wave File)
Firmware Analysis
- binwalk - Binwalk is a fast, easy to use tool for analyzing, reverse engineering, and extracting firmware images.
- FAT - is a toolkit built in order to help security researchers analyze and identify vulnerabilities in IoT and embedded device firmware.
- Firmware Modification Kit - is a collection of scripts and utilities to extract and rebuild linux based firmware images.
- Firmwalker - is a script for searching the extracted firmware file system for goodies!
Setup or Overlay Unpackers / Extractors
- innounp - the Inno Setup Unpacker.
- Universal Extractor 2 (UniExtract2) - is a tool designed to extract files from any type of extractable file.
- lessmsi - a tool to view and extract the contents of an Windows Installer (.msi) file.
- FUU - [F]aster [U]niversal [U]npacker.
Binary PE Analysis / Editor (Windows)
- ProtectionID - Great little tool to scan a Windows binary payload for overlays and packers. File:ProtectionId.690.December.2017.zip VT link, pw: recessim.com
- RDG Packer Detector - is a detector for packers, cryptors, compilers, installers.
- PE-bear - is a Portable Executable reversing tool with a friendly GUI using the Capstone Engine and is Open Source!
- CFF Explorer - is a PE editor called CFF Explorer and a process viewer with a lot of features.
Pattern Matching
- Yara - is a pattern matching swiss knife in the IT Security Researchers branch.
IAT Reconstructors (Windows)
- NtQuery Scylla - is a Windows Portable Executable imports reconstructor Open Source and part of x64dbg.
API monitoring ring3 (Windows)
- WinAPIOverride - is an advanced api monitoring software for 32 and 64 bits processes. You can monitor and/or override any function of a process.
- Rohitab API Monitor - is a free software that lets you monitor and control API calls made by applications and services. Its a powerful tool for seeing how applications and services work or for tracking down problems that you have in your own applications.
- tiny_tracer - is a Pin Tool for tracing API calls including parameters of selected functions, selected instructions RDTSC, CPUID, INT, inline system calls inc parameters of selected syscalls and more.
Debugger / disassembler for unmanged binaries
- Binary Ninja - reverse-engineering platform that can disassemble a binary and display the disassembly in linear or graph views.
- Ghidra - Ghidra is an open source software reverse engineering (SRE) framework developed by NSA's Research Directorate for NSA's cybersecurity mission.
- Ghidra Scripts/Plugins/Extension
- Scripts/Plugins/Extension - A curated list of awesome Ghidra materials.
- Ghidra Scripts/Plugins/Extension
- IDA - The IDA Disassembler and Debugger is an interactive, programmable, extensible, multi-processor disassembler hosted on Windows, Linux, or Mac OS X.
- IDA Scripts/Plugins/Extension
- IDA ARM - This script will give you the list of ARM system instructions used in your IDA database. This is useful for locating specific low-level pieces of code (setting up the MMU, caches, fault handlers, etc.).
- Keypatch - A multi-architeture assembler for IDA. Keypatch allows you enter assembly instructions to directly patch the binary under analysis. Powered by Keystone engine.
- IDAStealth - is a plugin which aims to hide the IDA debugger from most common anti-debugging techniques. The plugin is composed of two files, the plugin itself and a dll which is injected into the debugger as soon as the debugger attaches to the process.
- ida-sploiter - is a exploit development and vulnerability research tool. Some of the plugin's features include a powerful ROP gadgets search engine, semantic gadget analysis and filtering, interactive ROP chain builder, stack pivot analysis, writable function pointer search, cyclic memory pattern generation and offset analysis, detection of bad characters and memory holes, and many others.
- IDAtropy -is a plugin for Hex-Ray's IDA Pro designed to generate charts of entropy and histograms using the power of idapython and matplotlib
- Localxrefs - Finds references to any selected text from within the current function.
- Labeless - is a plugin system for dynamic, seamless and realtime synchronization between IDA Database and Olly. Labels, function names and global variables synchronization is supported. Olly and x64dbg are supported.
- Turbodiff - is a binary diffing tool developed as an IDA plugin. It discovers and analyzes differences between the functions of two binaries.
- A list of IDA Plugins (click here for more) - A large list/collection of plugins for IDA.
- IDA Scripts/Plugins/Extension
- Vivisect - Vivisect binary analysis framework. Includes Disassembler, Debugger, Emulation and Symbolik analysis engines. Includes built-in Server and Shared-Workspace functionality. Runs interactive or headless, programmable, extensible, multi-processor disassembler hosted on Windows, Linux, or Mac OS X (Pure-Python, using ctypes to access underlying OS debug mechanism). Supports RevSync via plugin, allowing basic collaboration with Binja, Ghidra, and IDA. Criticisms (from a core dev): "Graph View could use some work, slower than Binja and IDA (due to Python), documentation like an OpenSource Project... but we keep working to make it better. PR's and suggestions welcome." Best installed via Pip:
python3 -m pip install vivisect
- Veles - Open source tool for binary data analysis (No longer actively developed).
- Immunity Debugger - is a powerful new way to write exploits, analyze malware, and reverse engineer Windows binary files (python support)
- Hopper - Hopper can use LLDB or GDB, which lets you debug and analyze the binary in a dynamic way (only for Mac and Linux hosts, not for mobile devices).
- x64dbg - Is a powerful Open Source Ollydbg replacement with a User Interface very similar to Ollydbg also x64dbg as the name states offers x64 support.
- x64dbg Plugins/Integrations/Templates
- x64dbg's Wiki - is a wiki of Integrations and Plugins of x64dbg debugger.
- x64dbg Plugins/Integrations/Templates
- Reko - Reko is a binary decompiler for static analysis (ARM, x86-64, M68K, Aarch65, RISC-V and dotnet)
- radare2 and Rizin - radare2 and its fork Rizin are open source reverse engineering frameworks. Both are primarily used through a shell-like text UI, but also offer GUIs called iaito and Cutter respectively.
Debugging and Profiling dynamic analysis (Linux)
- valgrind - Valgrind is a GPL'd system for debugging and profiling Linux programs. With Valgrind's tool suite you can automatically detect many memory management and threading bugs, avoiding hours of frustrating bug-hunting, making your programs more stable.
- jTracer - is a stack trace visualization utility for libcsdbg. In other words, it acts as a TCP/IP server for libcsdbg clients, that connect to it and transfer their trace data, either C++ exception stack traces or generic thread stack traces and whole process stack dumps.
Debugger / disassembler for manged binaries
.NET
- dnSpy - is a debugger and .NET assembly editor. You can use it to edit and debug assemblies even if you don't have any source code available.
- Iced - Blazing fast and correct x86/x64 disassembler, assembler, decoder, encoder for Rust, .NET, Java, Python, Lua.
- ILSpy - NET Decompiler with support for PDB generation, ReadyToRun, Metadata (&more) - cross-platform!
- Telerik JustDecompile - is a free .NET decompiler and assembly browser that makes high-quality .NET decompilation easy With an open source decompilation engine.
- dotNET Tracer 2.0 by Kurapika - is a simple tool that has a similar functionality to RegMon or FileMon but it's designed to trace events in .NET assemblies in runtime. File:KDT2.0.zip VT1 VT2 (thermida packed), pw: recessim.com
- .NET deobfuscators
- de4dot CEx - is a deobfuscator based on de4dot with full support for vanilla ConfuserEx.
- de4dot - is a .NET deobfuscator and unpacker.
JAVA
- Jadx - Dex to Java decompiler. Command-line and GUI tools for producing Java source code from Android Dex and apk files.
- Recaf - Recaf is an open-source Java bytecode editor that simplifies the process of editing compiled Java applications.
- JEB decompiler - Decompile and debug Android dalvik, Intel x86, ARM, MIPS, RISC-V, S7 PLC, Java, WebAssembly & Ethereum Decompilers.
- APKinspector - is a powerful GUI tool for analysts to analyze the Android applications.
- Apktool - A tool for reverse engineering Android apk files.
- Bytecode viewer - A Java 8+ Jar & Android APK Reverse Engineering Suite (Decompiler, Editor, Debugger & More)
- Java deobfuscators
- deobfuscator - is a project that aims to deobfuscate most commercially-available obfuscators for Java. GUI version github
- Another Deobfuscator - Some deobfuscator for java. Supports superblaubeere27 / JObf / sb27, Paramorphism 2.1.2_9, Caesium, Monsey, Skid/qProtect, Scuti, CheatBreaker, Bozar, ...
PYTHON
- uncompyle6 - is a native Python cross-version decompiler and fragment decompiler. The successor to decompyle, uncompyle, and uncompyle2.
- pycdc - is a C++ python bytecode disassembler and decompiler.
PC platform exploration frameworks
- Chipsec - is a framework for analyzing the security of PC platforms including hardware, system firmware (BIOS/UEFI), and platform components. It includes a security test suite, tools for accessing various low level interfaces, and forensic capabilities.
- Metasploit Framework - is a Framework is a Ruby-based, modular penetration testing platform that enables you to write, test, and execute exploit code.
- Arachni - is a feature-full, modular, high-performance Ruby framework aimed towards helping penetration testers and administrators evaluate the security of web applications.
- Burp Suite - Burp or Burp Suite is a set of tools used for penetration testing of web applications.
Mobile exploration frameworks
- Frida - Dynamic instrumentation toolkit for developers, reverse-engineers, and security researchers.
- objection - is a runtime mobile exploration toolkit, powered by Frida, built to help you assess the security posture of your mobile applications, without needing a jailbreak.
- AppAudit - is an efficient program analysis tool that detects data leaks in mobile applications. It can accurately find all leaks within seconds and ~200 MB memory.
- LSposed - is a Riru / Zygisk module trying to provide an ART hooking framework which delivers consistent APIs with the OG Xposed, leveraging LSPlant hooking framework.
- LSPosed Module Repository
- Xposed Modules Repo - New Xposed(LSPosed) Module Repository.
- LSPosed Module Repository
- Xposed Framework - is a framework for mobile exploration hooking and modifying code on the fly. Inline API hooking example.
- Xposed modules
- JustTrustMe - Art framework hook to patch okHTTP and other common libs to fool the CERT chain in order for Mitmproxy to capture TLS traffic in cleartext.
- FakeXposed - Hide xposed, root, file redirection, two-way shielding data detection.
- SSLUnpinning_Xposed - Android Xposed Module to bypass SSL certificate validation (Certificate Pinning)..
- Xposed modules
- Xposed Framework API Development Documentation
- Xposed API Reference - Javadoc reference of the Xposed Framework API. It's meant for module developers who want to understand which classes and methods they can use.
- Xposed Framework API Development Documentation
Promiscuous mode eavesdropping TCP/UDP
- mitmproxy - is an interactive TLS-capable intercepting HTTP proxy for penetration testers and software developers.
- wireshark - is a network traffic analyzer, or "sniffer", for Linux, macOS, *BSD and other Unix and Unix-like operating systems and for Windows.
- Zed Attack Proxy (ZAP) - is an Open Source & easy to use integrated penetration testing tool for finding vulnerabilities in web applications.
- Mallet - is an intercepting proxy for arbitrary protocols.
- PETEP (PEnetration TEsting Proxy) - is an open-source Java application for traffic analysis & modification using TCP/UDP proxies. PETEP is a useful tool for performing penetration tests of applications with various application protocols.
HTTP(S) Debuggers / Web Debuggers
- HTTP Toolkit - is a beautiful, cross-platform & open-source HTTP(S) debugging proxy, analyzer & client, with built-in support for modern tools from Docker to Android to GraphQL.
- httpry - is a HTTP logging and information retrieval tool written in Perl and C.
- Requestly - Bring the power of Charles Proxy, Fiddler & Postman together with beautiful, modern UI & collaboration features.
- Fiddler - is a Web Debugger is a serviceable web debugging proxy for logging all HTTP(S) traffic linking your computer and the internet, allowing for traffic inspection, breakpoint setting, and more.
Other Network Tools
- tcpview - is a tool that will enumerate all active TCP and UDP endpoints, resolving all IP addresses to their domain name versions (Windows).
- cports - is network monitoring software that displays the list of all currently opened TCP/IP and UDP ports on your local Windows computer.
- NetworkMiner - is an open source network forensics tool that extracts artifacts, such as files, images, emails and passwords, from captured network traffic in PCAP files.
- netstat - is a Linux CLI tool to print network connections, routing tables, interface statistics, masquerade connections, and multicast memberships.
Unified Extensible Firmware Interface (UEFI) & legacy PC BIOS Tools
- UEFI
- UEFITool / UEFIExtract / UEFIFind - is a UEFI firmware image viewer and editor.
- IFRExtractor-RS - is a Rust utility to extract UEFI IFR (Internal Form Representation) data found in a binary file into human-readable text.
- uefi-firmware-parser - is a cross-platform open source application written in Python. Very tinker-friendly. Can be used in scripts to automate firmware patching.
- AMIBCP_5.01_x64 - AMI BIOS Configuration Program (AMIBCP) is a powerful customization utility that enables OEMs/ODMs to customize the Aptio® ROM image without intervening on the source code. VT link
- AMIBCP 5.01.0014 x64 VT link
- AMIBCP_5.02.0023 VT link
- AMIBCP_5.02.0031 VT link
- AMIBCP 5.02.0034 VT link
- UEFI
- BIOS
- PhoenixTool - is a Windows-only freeware GUI application written in C#. Used mostly for SLIC-related modifications, but it not limited to this task. Requires Microsoft .NET 3.5 to work properly. Supports unpacking firmware images from various vendor-specific formats like encrypted HP update files and Dell installers.
- AMI
- AMIBCP_2.25 VT link
- AMIBCP_2.43 VT link
- AMIBCP_3.13 VT link
- AMIBCP_3.37 VT link
- AMIBCP_3.46 VT link
- AMIBCP_3.47 VT link
- AMIBCP_3.51 VT link
- AMIBCP_4.53 VT link
- AMIBCP_4.55 VT link
- MMTOOL_2.22.1 - MMtool stands for Module Management Tool. As one of AMI's BIOS/UEFI utilities, MMTool allows users to manage firmware file modules within the Aptio ROM image. VT link
- MMTOOL_3.12 VT link
- MMTOOl_3.19 VT link
- MMTOOL_3.19_Mod_21FiX VT link
- MMTOOL_3.22 VT link
- MMTOOL_3.22_1B_21Fix-BKMOD VT link
- MMTOOL_3.22_CN_BKMod VT link
- MMTOOL_3.23_CN_BKMod VT link
- MMTOOL_3.26 VT link
- MMTOOL_4.50.0.23VT link
- MMTOOL_5.0.07 VT link
- MMTOOL_5.02.0024 VT link
- MMTOOL_5.02.0025 VT link
- Award
- Award Bios Editor - is a editor for Award bios.
- Insyde
- H2OEZE_x86_WIN_100.00.02.13 - H2OEZE™: Easy BIOS Editor that helps edit binaries in the BIOS, including Option ROMs, driver binaries, logos, and Setup values. VT link
- H2OEZE_x86_WIN_100.00.03.04 VT link
- H2OEZE_x64_WIN_100.00.03.04 VT link
- BIOS
- Download all* tools in one archive, click here. VT link
Operating System for Penetration Testing & Digital Forensics
- Kali Linux - is an open-source, Debian-based Linux distribution geared towards various information security tasks, such as Penetration Testing, Security Research, Computer Forensics and Reverse Engineering.
- BlackBox is more than an operating system, it is a Free Open Source Community Project with the aim of promoting the culture of security in IT environment and give its contribution to make it better and safer.
- BlackArch - is an Arch Linux-based penetration testing distribution for penetration testers and security researchers.
- Parrot Security - is based on top of Debian, the most advanced and recognized universal operating system that can run anywhere.
- Fedora Security Spin - is a live media based on Fedora to provide a safe test environment for working on security auditing, forensics and penetration testing, coupled with all the Fedora Security features and tools.
- CAINE - CAINE (Computer Aided INvestigative Environment) is an Italian GNU/Linux live distribution created as a Digital Forensics project.
- Dracos Linux - is the Linux operating system from Indonesia, open source is built based on Debian live project under the protection of the GNU General Public License v3.0. This operating system is one variant of Linux distributions, which is used to perform security testing (penetration testing). Dracos linux in Arm by hundreds hydraulic pentest, forensics and reverse engineering.
- Pentoo - is a Live CD and Live USB designed for penetration testing and security assessment. Based off Gentoo Linux, Pentoo is provided both as 32 and 64 bit installable livecd.
Privacy Operating System
- Tails - is a portable operating system that protects against surveillance and censorship.
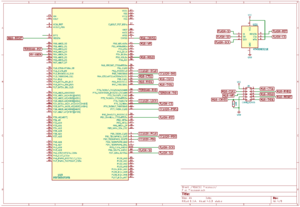
Tools for opening CAD or Boardview files
Description: Boardview is a type of file containing information about printed circuit boards, their components, used signals, test points and more. These files may have following extensions: .asc, .bdv, .brd, .bv, .cad, .cst, .gr, .f2b, .fz, .tvw and others.
- FlexBV - Advanced FlexBV boardview software integrates your boardview files with PDF schematics to substantially ease the process of tracking down faults and understanding damaged boards
- OpenBoardView - is a Open Source Linux SDL/ImGui edition software for viewing .brd files, intended as a drop-in replacement for the "Test_Link" software and "Landrex".
- BoardViewer - BoardViewer is software intended for viewing various boardview file types
- CADview - simple old tool for viewing CAD files of PCB's. File:CAD View.zip VT link
For resources to open in your favorite boardview program visit Literature -> 1.2 Datasheets boardviews & schematics
Education
Tools are great, and sometimes free! Without knowing how to use them, they can be a big waste of time. Better to spend your time learning the basics, then apply your knowledge.
Reverse Engineering Tutorial - A comprehensive reverse engineering tutorial covering x86, x64, 32-bit ARM & 64-bit ARM architectures.
File:Reverse Engineering Malware IDA & Olly Basics 5 parts by otw v1.pdf - A Reverse Engineering Malware introduction and bare basics IDA & Olly x86 (5 parts) by otw.
Some publicly available Malware analysis and Reverse engineering - is a curated list of awesome materials from the user Dump-GUY a former Forensic, Malware Analyst, Reverse Engineer). Youtube channel.
Reversing / Malware Analysis / Assembly -resources - is a large list of reversing materials and courses.
Malware and Reverse Engineering Complete Collection - Awesome Malware and Reverse Engineering collection by Joas.