Software Tools
Disassemblers, Decompilers, Development Tools, Schematic/PCB Capture and other reverse engineering software. If you used it while reverse engineering, list it here!
Contents
- 1 Tool Index
- 1.1 RF Signals Analysis
- 1.2 Firmware Analysis
- 1.3 Setup or Overlay Unpackers / Extractors
- 1.4 Binary PE Analysis / Editor (Windows)
- 1.5 IAT Reconstructors (Windows)
- 1.6 API monitoring ring3 (Windows)
- 1.7 Debugger / disassembler for unmanged binaries
- 1.8 Debugging and Profiling dynamic analysis (Linux)
- 1.9 Debugger / disassembler for manged binaries
- 1.10 Mobile exploration frameworks
- 1.11 Tools for opening CAD or Boardview files
- 2 Education
Tool Index
RF Signals Analysis
- Universal Radio Hacker - tool to analyze and extract data from SDR-captured radio signals (especially pilots, ISM RF devices, etc). See youtube for tutorials and examples.
- GNU Radio - toolkit that provides signal processing blocks to implement software-defined radios and signal processing systems.
- Audacity - is a audio editor that can be used to cleanup the radio waves captured by a SDR or Software Defined Radio. (Example: Start Audacity -> Import –> Raw Data -> Radio Wave File)
Firmware Analysis
- binwalk - Binwalk is a fast, easy to use tool for analyzing, reverse engineering, and extracting firmware images.
- FAT - is a toolkit built in order to help security researchers analyze and identify vulnerabilities in IoT and embedded device firmware.
- Firmware Modification Kit - is a collection of scripts and utilities to extract and rebuild linux based firmware images.
- Firmwalker - is a script for searching the extracted firmware file system for goodies!
Setup or Overlay Unpackers / Extractors
- innounp - the Inno Setup Unpacker.
- Universal Extractor 2 (UniExtract2) - is a tool designed to extract files from any type of extractable file.
- lessmsi - a tool to view and extract the contents of an Windows Installer (.msi) file.
- FUU - [F]aster [U]niversal [U]npacker.
Binary PE Analysis / Editor (Windows)
- ProtectionID - Great little tool to scan a Windows binary payload for overlays and packers. File:ProtectionId.690.December.2017.zip VT link, pw: recessim.com
- RDG Packer Detector - is a detector for packers, cryptors, compilers, installers.
- PE-bear - is a Portable Executable reversing tool with a friendly GUI using the Capstone Engine and is Open Source!
- CFF Explorer - is a PE editor called CFF Explorer and a process viewer with a lot of features.
IAT Reconstructors (Windows)
- NtQuery Scylla - is a Windows Portable Executable imports reconstructor open source and part of x64dbg.
API monitoring ring3 (Windows)
- WinAPIOverride - is an advanced api monitoring software for 32 and 64 bits processes. You can monitor and/or override any function of a process.
- Rohitab API Monitor - is a free software that lets you monitor and control API calls made by applications and services. Its a powerful tool for seeing how applications and services work or for tracking down problems that you have in your own applications.
Debugger / disassembler for unmanged binaries
- Binary Ninja - reverse-engineering platform that can disassemble a binary and display the disassembly in linear or graph views.
- Ghidra - Ghidra is an open source software reverse engineering (SRE) framework developed by NSA's Research Directorate for NSA's cybersecurity mission.
- IDA - The IDA Disassembler and Debugger is an interactive, programmable, extensible, multi-processor disassembler hosted on Windows, Linux, or Mac OS X.
- Vivisect - Vivisect binary analysis framework. Includes Disassembler, Debugger, Emulation and Symbolik analysis engines. Includes built-in Server and Shared-Workspace functionality. Runs interactive or headless, programmable, extensible, multi-processor disassembler hosted on Windows, Linux, or Mac OS X (Pure-Python, using ctypes to access underlying OS debug mechanism). Supports RevSync via plugin, allowing basic collaboration with Binja, Ghidra, and IDA. Criticisms (from a core dev): "Graph View could use some work, slower than Binja and IDA (due to Python), documentation like an OpenSource Project... but we keep working to make it better. PR's and suggestions welcome." Best installed via Pip:
python3 -m pip install vivisect
- Veles - Open source tool for binary data analysis (No longer actively developed).
- Immunity Debugger - is a powerful new way to write exploits, analyze malware, and reverse engineer Windows binary files (python support)
- Hopper - Hopper can use LLDB or GDB, which lets you debug and analyze the binary in a dynamic way (only for Mac and Linux hosts, not for mobile devices).
- x64dbg - Is a powerful Open Source Ollydbg replacement with a User Interface very similar to Ollydbg also x64dbg as the name states offers x64 support.
- Reko - Reko is a binary decompiler for static analysis (ARM, x86-64, M68K, Aarch65, RISC-V and dotnet)
Debugging and Profiling dynamic analysis (Linux)
- valgrind - Valgrind is a GPL'd system for debugging and profiling Linux programs. With Valgrind's tool suite you can automatically detect many memory management and threading bugs, avoiding hours of frustrating bug-hunting, making your programs more stable.
- jTracer - is a stack trace visualization utility for libcsdbg. In other words, it acts as a TCP/IP server for libcsdbg clients, that connect to it and transfer their trace data, either C++ exception stack traces or generic thread stack traces and whole process stack dumps.
Debugger / disassembler for manged binaries
.NET
- dnSpy - is a debugger and .NET assembly editor. You can use it to edit and debug assemblies even if you don't have any source code available.
- ILSpy - NET Decompiler with support for PDB generation, ReadyToRun, Metadata (&more) - cross-platform!
- Telerik JustDecompile - is a free .NET decompiler and assembly browser that makes high-quality .NET decompilation easy With an open source decompilation engine.
- dotNET Tracer 2.0 by Kurapika - is a simple tool that has a similar functionality to RegMon or FileMon but it's designed to trace events in .NET assemblies in runtime. File:KDT2.0.zip VT1 VT2 (thermida packed), pw: recessim.com
JAVA
- Jadx - Dex to Java decompiler. Command-line and GUI tools for producing Java source code from Android Dex and apk files.
- Recaf - Recaf is an open-source Java bytecode editor that simplifies the process of editing compiled Java applications.
- JEB decompiler - Decompile and debug Android dalvik, Intel x86, ARM, MIPS, RISC-V, S7 PLC, Java, WebAssembly & Ethereum Decompilers.
- APKinspector - is a powerful GUI tool for analysts to analyze the Android applications.
- Apktool - A tool for reverse engineering Android apk files.
- Bytecode viewer - A Java 8+ Jar & Android APK Reverse Engineering Suite (Decompiler, Editor, Debugger & More)
PYTHON
- uncompyle6 - is a native Python cross-version decompiler and fragment decompiler. The successor to decompyle, uncompyle, and uncompyle2.
- pycdc - is a C++ python bytecode disassembler and decompiler.
Mobile exploration frameworks
- Frida - Dynamic instrumentation toolkit for developers, reverse-engineers, and security researchers.
- objection - is a runtime mobile exploration toolkit, powered by Frida, built to help you assess the security posture of your mobile applications, without needing a jailbreak.
- Xposed Framework - is a framework for mobile exploration hooking and modifying code on the fly. Inline API hooking example.
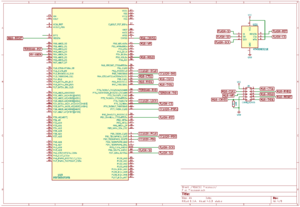
Tools for opening CAD or Boardview files
Description: Boardview is a type of file containing information about printed circuit boards, their components, used signals, test points and more. These files may have following extensions: .asc, .bdv, .brd, .bv, .cad, .cst, .gr, .f2b, .fz, .tvw and others.
- FlexBV - Advanced FlexBV boardview software integrates your boardview files with PDF schematics to substantially ease the process of tracking down faults and understanding damaged boards
- BoardViewer - BoardViewer is software intended for viewing various boardview file types
- CADview - simple old tool for viewing CAD files of PCB's. File:CAD View.zip VT link
Education
Tools are great, and sometimes free! Without knowing how to use them, they can be a big waste of time. Better to spend your time learning the basics, then apply your knowledge.
Reverse Engineering Tutorial - A comprehensive reverse engineering tutorial covering x86, x64, 32-bit ARM & 64-bit ARM architectures.