Difference between revisions of "Hardware Exploits"
(Created page with "thumb|Equipment typically used while exploiting hardware. Exploits in hardware typically used to extract firmware or gain debug access...") |
|||
| (4 intermediate revisions by the same user not shown) | |||
| Line 1: | Line 1: | ||
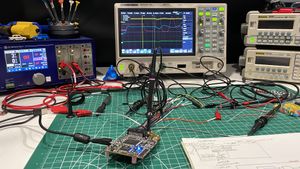
[[File:Lab Bench Hardware Exploit.jpg|thumb|Equipment typically used while exploiting hardware.]] | [[File:Lab Bench Hardware Exploit.jpg|thumb|Equipment typically used while exploiting hardware.]] | ||
| − | Exploits in hardware | + | Exploits in hardware used to extract firmware or gain debug access to locked microcontrollers. |
==Manufacturer Index== | ==Manufacturer Index== | ||
| + | [[Apex Microelectronics Exploits|Apex Microelectronics (APM)]]<br> | ||
| + | [[Atmel Exploits|Atmel (AT)]]<br> | ||
| + | [[China Key System Exploits|China Key System (CKS)]]<br> | ||
| + | [[GigaDevice Exploits|GigaDevice (GD)]]<br> | ||
| + | [[Microchip Exploits|Microchip]]<br> | ||
| + | [[STMicroelectronics Exploits|STMicroelectronics (STM)]]<br> | ||
Latest revision as of 22:16, 22 June 2023
Exploits in hardware used to extract firmware or gain debug access to locked microcontrollers.