Difference between revisions of "Software Tools"
Polymorphic7 (talk | contribs) m (typo) |
Polymorphic7 (talk | contribs) (Major update) |
||
| Line 129: | Line 129: | ||
---- | ---- | ||
| + | |||
| + | ====PC platform exploration frameworks==== | ||
| + | |||
| + | *[https://github.com/chipsec/chipsec Chipsec] - is a framework for analyzing the security of PC platforms including hardware, system firmware (BIOS/UEFI), and platform components. It includes a security test suite, tools for accessing various low level interfaces, and forensic capabilities. | ||
| + | |||
| + | *[https://github.com/rapid7/metasploit-framework Metasploit Framework] - is a Framework is a Ruby-based, modular penetration testing platform that enables you to write, test, and execute exploit code. | ||
| + | |||
| + | *[https://github.com/Arachni/arachni Arachni] - is a feature-full, modular, high-performance Ruby framework aimed towards helping penetration testers and administrators evaluate the security of web applications. | ||
| + | |||
| + | |||
====Mobile exploration frameworks==== | ====Mobile exploration frameworks==== | ||
| Line 135: | Line 145: | ||
*[https://github.com/sensepost/objection objection] - is a runtime mobile exploration toolkit, powered by Frida, built to help you assess the security posture of your mobile applications, without needing a jailbreak. | *[https://github.com/sensepost/objection objection] - is a runtime mobile exploration toolkit, powered by Frida, built to help you assess the security posture of your mobile applications, without needing a jailbreak. | ||
| + | |||
| + | *[https://github.com/mingyuan-xia/AppAudit AppAudit] - is an efficient program analysis tool that detects data leaks in mobile applications. It can accurately find all leaks within seconds and ~200 MB memory. | ||
| + | |||
| + | *[https://github.com/LSPosed/LSPosed LSposed] - is a Riru / Zygisk module trying to provide an ART hooking framework which delivers consistent APIs with the OG Xposed, leveraging LSPlant hooking framework. | ||
*[https://github.com/ElderDrivers/EdXposed Xposed Framework] - is a framework for mobile exploration hooking and modifying code on the fly. [https://binderfilter.github.io/xposed/ Inline API hooking example]. | *[https://github.com/ElderDrivers/EdXposed Xposed Framework] - is a framework for mobile exploration hooking and modifying code on the fly. [https://binderfilter.github.io/xposed/ Inline API hooking example]. | ||
| + | :: Xposed modules | ||
| + | :::*[https://github.com/Fuzion24/JustTrustMe JustTrustMe] - Art framework hook to patch okHTTP and other common libs to fool the CERT chain in order for Mitmproxy to capture TLS traffic in cleartext. | ||
| + | :::*[https://github.com/sanfengAndroid/FakeXposed FakeXposed] - Hide xposed, root, file redirection, two-way shielding data detection. | ||
| + | |||
| + | |||
| + | ====Promiscuous mode eavesdropping TCP/UDP==== | ||
| + | ::*[https://github.com/mitmproxy/mitmproxy mitmproxy] - is an interactive TLS-capable intercepting HTTP proxy for penetration testers and software developers. | ||
| + | |||
| + | ::*[https://gitlab.com/wireshark/wireshark wireshark] - is a network traffic analyzer, or "sniffer", for Linux, macOS, *BSD and other Unix and Unix-like operating systems and for Windows. | ||
| + | |||
| + | ::*[https://github.com/SensePost/Mallet Mallet] - is an intercepting proxy for arbitrary protocols. | ||
---- | ---- | ||
| + | ====Unified Extensible Firmware Interface (UEFI) & legacy PC BIOS Tools==== | ||
| + | ::'''UEFI''' | ||
| + | ::*[https://github.com/LongSoft/UEFITool UEFITool / UEFIExtract / UEFIFind] - is a UEFI firmware image viewer and editor. | ||
| + | ::*[https://github.com/LongSoft/IFRExtractor-RS IFRExtractor-RS] - is a Rust utility to extract UEFI IFR (Internal Form Representation) data found in a binary file into human-readable text. | ||
| + | ::*[https://github.com/direstraits96/BIOS-MOD-TOOLS/blob/main/AMI/AMIBCP/AMIBCP_5.01_x64.exe AMIBCP_5.01_x64] - is a tool from the manufacturer AMI (American Megatrends International) to modify the BIOS bin file with. [https://www.virustotal.com/gui/file/58f822028c24bb452e4c0af60118b3db2a492d91dbf477960ac4f595cfded91b VT link] | ||
| + | ::*[https://github.com/tylernguyen/razer15-hackintosh/blob/master/tools/AMIBCP64/AMIBCP64.exe AMIBCP 5.01.0014 x64] [https://www.virustotal.com/gui/file/58f822028c24bb452e4c0af60118b3db2a492d91dbf477960ac4f595cfded91b/details VT link] | ||
| + | ::*[https://github.com/direstraits96/BIOS-MOD-TOOLS/blob/main/AMI/AMIBCP/AMIBCP_5.02.0023.exe AMIBCP_5.02.0023] [https://www.virustotal.com/gui/file/38f7c54098af1544ddba6324e6d1fea6d1462f422ba021f309ad4445dacd0467 VT link] | ||
| + | ::*[https://github.com/direstraits96/BIOS-MOD-TOOLS/blob/main/AMI/AMIBCP/AMIBCP_5.02.0031.exe AMIBCP_5.02.0031] [https://www.virustotal.com/gui/file/c7ade67fe0e8f4c22f73ce3168ff6e718086f1eda83cce4c065b4fe49bd5ad99 VT link] | ||
| + | ::*[https://github.com/direstraits96/BIOS-MOD-TOOLS/blob/main/AMI/AMIBCP/AMIBCP%205.02.0034.exe AMIBCP 5.02.0034][https://www.virustotal.com/gui/file/7fe28fb8a7419c95fba428891e5b3914d9e2b365a5a8932da74db52a1c1dabd8 VT link] | ||
| + | |||
| + | ::'''BIOS''' | ||
| + | ::'''AMI''' | ||
| + | ::*[https://github.com/direstraits96/BIOS-MOD-TOOLS/blob/main/AMI/AMIBCP/AMIBCP_2.25.zip AMIBCP_2.25] - AMI BIOS Configuration Program (AMIBCP) is a powerful customization utility that enables OEMs/ODMs to customize the Aptio® ROM image without intervening on the source code. [https://www.virustotal.com/gui/file/71050f3db40cc6c0a623d66c8eeb05d0a0818226fd11ed787452f4f540d45204 VT link] | ||
| + | ::*[https://github.com/direstraits96/BIOS-MOD-TOOLS/blob/main/AMI/AMIBCP/AMIBCP_2.43.zip AMIBCP_2.43] [https://www.virustotal.com/gui/file/efa10cfe5f78c16982abf458eb50a4fde152631ad3b77838bd2013a763045ced VT link] | ||
| + | ::*[https://github.com/direstraits96/BIOS-MOD-TOOLS/blob/main/AMI/AMIBCP/AMIBCP_3.13.exe AMIBCP_3.13] [https://www.virustotal.com/gui/file/e0a5b1059f04813e72c6d4fa639d32567002fdd86321895b5987224a4518896e VT link] | ||
| + | ::*[https://github.com/direstraits96/BIOS-MOD-TOOLS/blob/main/AMI/AMIBCP/AMIBCP_3.37.exe AMIBCP_3.37] [https://www.virustotal.com/gui/file/1174e177b28fb7ecbac6c5043a9e8d78ff4756f657ea72369c5fb6b43b1f2623 VT link] | ||
| + | ::*[https://github.com/direstraits96/BIOS-MOD-TOOLS/blob/main/AMI/AMIBCP/AMIBCP_3.46.exe AMIBCP_3.46] [https://www.virustotal.com/gui/file/84bd5b151286d4181ef26284d96ca49074e18574b8454c51cb0b34013ee5d073 VT link] | ||
| + | ::*[https://github.com/direstraits96/BIOS-MOD-TOOLS/blob/main/AMI/AMIBCP/AMIBCP_3.47.exe AMIBCP_3.47] [https://www.virustotal.com/gui/file/20d93c6f868d4638676b7cde2c66c5589433c1480250aa0d774c4feef3337507 VT link] | ||
| + | ::*[https://github.com/direstraits96/BIOS-MOD-TOOLS/blob/main/AMI/AMIBCP/AMIBCP_3.51.exe AMIBCP_3.51] [https://www.virustotal.com/gui/file/0d630b4b9c34d6c7132249a1a7bc3de33b39779fc90d9a367272cf57b4621aed VT link] | ||
| + | ::*[https://github.com/direstraits96/BIOS-MOD-TOOLS/blob/main/AMI/AMIBCP/AMIBCP_4.53.exe AMIBCP_4.53] [https://www.virustotal.com/gui/file/3f90e402dab9f64cbc4514e18bc2625ec7672da806cd9e0ef2e803b0ce104a01 VT link] | ||
| + | ::*[https://github.com/direstraits96/BIOS-MOD-TOOLS/blob/main/AMI/AMIBCP/AMIBCP_4.55.exe AMIBCP_4.55] [https://www.virustotal.com/gui/file/451ad821a66e9ea89ee0544ce53cfab887dc0bb662a2de95f0e1aa1663dc6e06 VT link] | ||
| + | ::*[https://github.com/direstraits96/BIOS-MOD-TOOLS/blob/main/AMI/MMTOOL/MMTOOL_2.22.1.exe MMTOOL_2.22.1] - MMtool stands for Module Management Tool. As one of AMI's BIOS/UEFI utilities, MMTool allows users to manage firmware file modules within the Aptio ROM image. [https://www.virustotal.com/gui/file/cf49f1e742f5cce68152f3c17df29e5c9aa7fb557c432402199159ffda44e007 VT link] | ||
| + | ::*[https://github.com/direstraits96/BIOS-MOD-TOOLS/blob/main/AMI/MMTOOL/MMTOOL_3.12.exe MMTOOL_3.12] [https://www.virustotal.com/gui/file/78c3ca427878be5b07058f422914027462d3ac740b0de247169cc0aee4195e3b VT link] | ||
| + | ::*[https://github.com/direstraits96/BIOS-MOD-TOOLS/blob/main/AMI/MMTOOL/MMTOOl_3.19.exe MMTOOl_3.19] [https://www.virustotal.com/gui/file/b4b30c6ff911f18d3383b094628f59aa5ec3b109acd12aaef391acf9720e52af VT link] | ||
| + | ::*[https://github.com/direstraits96/BIOS-MOD-TOOLS/blob/main/AMI/MMTOOL/MMTOOL_3.19_Mod_21FiX.exe MMTOOL_3.19_Mod_21FiX] [https://www.virustotal.com/gui/file/66e2717fcac67b073d24916c74bc8d8dd7932b188d20b8b635b511e6195d5855 VT link] | ||
| + | ::*[https://github.com/direstraits96/BIOS-MOD-TOOLS/blob/main/AMI/MMTOOL/MMTOOL_3.22.EXE MMTOOL_3.22] [https://www.virustotal.com/gui/file/5616a62d2b50a53490bb705b769ed86bf4b49799663a814fcd1284ebc0bdc62f VT link] | ||
| + | ::*[https://github.com/direstraits96/BIOS-MOD-TOOLS/blob/main/AMI/MMTOOL/MMTOOL_3.22_1B_21Fix-BKMOD.EXE MMTOOL_3.22_1B_21Fix-BKMOD] [https://www.virustotal.com/gui/file/5616a62d2b50a53490bb705b769ed86bf4b49799663a814fcd1284ebc0bdc62f VT link] | ||
| + | ::*[https://github.com/direstraits96/BIOS-MOD-TOOLS/blob/main/AMI/MMTOOL/MMTOOL_3.22_CN_BKMod.exe MMTOOL_3.22_CN_BKMod] [https://www.virustotal.com/gui/file/f467d75962278a4e01d646cdf8008136912d8a1ddd588c45e2fcee9d7cd17140 VT link] | ||
| + | ::*[https://github.com/direstraits96/BIOS-MOD-TOOLS/blob/main/AMI/MMTOOL/MMTOOL_3.23_CN_BKMod.exe MMTOOL_3.23_CN_BKMod] [https://www.virustotal.com/gui/file/9bf846d023312c889069b03f5ab7157e270fc67c5d295e745d0a5f27d12a71de VT link] | ||
| + | ::*[https://github.com/direstraits96/BIOS-MOD-TOOLS/blob/main/AMI/MMTOOL/MMTOOL_3.26.exe MMTOOL_3.26] [https://www.virustotal.com/gui/file/c5a64ea7ce2bea8556fa81e0069adbba793181bfaa76f59f4f472f0a471bac98 VT link] | ||
| + | ::*[https://github.com/direstraits96/BIOS-MOD-TOOLS/blob/main/AMI/MMTOOL/MMTOOL_4.50.0.23.exe MMTOOL_4.50.0.23][https://www.virustotal.com/gui/file/7d0377a72e67e5a71400361416452440826832aeb2c9bebaa578e8af962eaafd VT link] | ||
| + | ::*[https://github.com/direstraits96/BIOS-MOD-TOOLS/blob/main/AMI/MMTOOL/MMTOOL_5.0.07.exe MMTOOL_5.0.07] [https://www.virustotal.com/gui/file/28049163fd1e3423c42b229a5f6ed877f14e7caf3b794bf7efb970b375e6ff41 VT link] | ||
| + | ::*[https://github.com/direstraits96/BIOS-MOD-TOOLS/blob/main/AMI/MMTOOL/MMTOOL_5.02.0024.exe MMTOOL_5.02.0024] [https://www.virustotal.com/gui/file/bbc3e75905997ddc05c523e57a72e49bbfcaf84dca64e460f10f8553b7fda9ee VT link] | ||
| + | ::*[https://github.com/direstraits96/BIOS-MOD-TOOLS/blob/main/AMI/MMTOOL/MMTOOL_5.02.0025.exe MMTOOL_5.02.0025] [https://www.virustotal.com/gui/file/5d05d0bbea720d4b73dc66db55031c2659458696b9f143df3b7e2f43040289cc VT link] | ||
| + | ::'''Award''' | ||
| + | ::*[https://github.com/direstraits96/BIOS-MOD-TOOLS/tree/main/Award_Bios_Editor Award Bios Editor] - is a editor for Award bios. | ||
| + | ::'''Insyde''' | ||
| + | ::*[https://github.com/direstraits96/BIOS-MOD-TOOLS/blob/main/Insyde/H2OEZE/x86/H2OEZE_x86_WIN_100.00.02.13.zip H2OEZE_x86_WIN_100.00.02.13] - H2OEZE™: Easy BIOS Editor that helps edit binaries in the BIOS, including Option ROMs, driver binaries, logos, and Setup values. [https://www.virustotal.com/gui/file/9660f1bf9436b258ec5ad857a94fbd0ec1f8fbff8ab22ca1dfcfb5ebbdcedf08 VT link] | ||
| + | ::*[https://github.com/direstraits96/BIOS-MOD-TOOLS/blob/main/Insyde/H2OEZE/x86/H2OEZE_x86_WIN_100.00.03.04.zip H2OEZE_x86_WIN_100.00.03.04] [https://www.virustotal.com/gui/file/2a1005803da854693502093445906eb2cccb24947d6828bc1533ba3603c73b0a VT link] | ||
| + | ::*[https://github.com/direstraits96/BIOS-MOD-TOOLS/blob/main/Insyde/H2OEZE/x64/H2OEZE_x64_WIN_100.00.03.04.rar H2OEZE_x64_WIN_100.00.03.04] [https://www.virustotal.com/gui/file/20d2d0336d30afd0b1961eb42dc061ce66a6fcfbfba1530e7abd9be883dcb45c VT link] | ||
| + | |||
| + | |||
| + | :Download all tools in one archive, [https://github.com/direstraits96/BIOS-MOD-TOOLS/archive/refs/heads/main.zip click here]. [VT link] | ||
| + | |||
| + | ---- | ||
| + | |||
| + | ====Operating System for Penetration Testing & Digital Forensics==== | ||
| + | |||
| + | *[https://www.kali.org/ Kali Linux] - is an open-source, Debian-based Linux distribution geared towards various information security tasks, such as Penetration Testing, Security Research, Computer Forensics and Reverse Engineering. | ||
| + | |||
| + | *[https://www.backbox.org/ BlackBox] is more than an operating system, it is a Free Open Source Community Project with the aim of promoting the culture of security in IT environment and give its contribution to make it better and safer. | ||
| + | |||
| + | *[https://blackarch.org/ BlackArch] - is an Arch Linux-based penetration testing distribution for penetration testers and security researchers. | ||
| + | |||
| + | *[https://www.parrotsec.org/ Parrot Security] - is based on top of Debian, the most advanced and recognized universal operating system that can run anywhere. | ||
| + | |||
| + | *[https://labs.fedoraproject.org/security/ Fedora Security Spin] - is a live media based on Fedora to provide a safe test environment for working on security auditing, forensics and penetration testing, coupled with all the Fedora Security features and tools. | ||
| + | |||
| + | *[https://www.caine-live.net/ CAINE] - CAINE (Computer Aided INvestigative Environment) is an Italian GNU/Linux live distribution created as a Digital Forensics project. | ||
| + | |||
| + | *[https://github.com/dracos-linux Dracos Linux] - is the Linux operating system from Indonesia, open source is built based on Debian live project under the protection of the GNU General Public License v3.0. This operating system is one variant of Linux distributions, which is used to perform security testing (penetration testing). Dracos linux in Arm by hundreds hydraulic pentest, forensics and reverse engineering. | ||
| + | |||
| + | *[https://www.pentoo.ch/ Pentoo] - is a Live CD and Live USB designed for penetration testing and security assessment. Based off Gentoo Linux, Pentoo is provided both as 32 and 64 bit installable livecd. | ||
| + | |||
| + | ====Privacy Operating System==== | ||
| + | |||
| + | *[https://tails.net/ Tails] - is a portable operating system that protects against surveillance and censorship. | ||
| + | |||
| + | |||
| + | ---- | ||
====Tools for opening CAD or Boardview files==== | ====Tools for opening CAD or Boardview files==== | ||
Revision as of 18:27, 8 October 2023
Disassemblers, Decompilers, Development Tools, Schematic/PCB Capture and other reverse engineering software. If you used it while reverse engineering, list it here!
Contents
- 1 Tool Index
- 1.1 RF Signals Analysis
- 1.2 Firmware Analysis
- 1.3 Setup or Overlay Unpackers / Extractors
- 1.4 Binary PE Analysis / Editor (Windows)
- 1.5 IAT Reconstructors (Windows)
- 1.6 API monitoring ring3 (Windows)
- 1.7 Debugger / disassembler for unmanged binaries
- 1.8 Debugging and Profiling dynamic analysis (Linux)
- 1.9 Debugger / disassembler for manged binaries
- 1.10 PC platform exploration frameworks
- 1.11 Mobile exploration frameworks
- 1.12 Promiscuous mode eavesdropping TCP/UDP
- 1.13 Unified Extensible Firmware Interface (UEFI) & legacy PC BIOS Tools
- 1.14 Operating System for Penetration Testing & Digital Forensics
- 1.15 Privacy Operating System
- 1.16 Tools for opening CAD or Boardview files
- 2 Education
Tool Index
RF Signals Analysis
- Universal Radio Hacker - tool to analyze and extract data from SDR-captured radio signals (especially pilots, ISM RF devices, etc). See youtube for tutorials and examples.
- GNU Radio - toolkit that provides signal processing blocks to implement software-defined radios and signal processing systems.
- Audacity - is a audio editor that can be used to cleanup the radio waves captured by a SDR or Software Defined Radio. (Example: Start Audacity -> Import –> Raw Data -> Radio Wave File)
Firmware Analysis
- binwalk - Binwalk is a fast, easy to use tool for analyzing, reverse engineering, and extracting firmware images.
- FAT - is a toolkit built in order to help security researchers analyze and identify vulnerabilities in IoT and embedded device firmware.
- Firmware Modification Kit - is a collection of scripts and utilities to extract and rebuild linux based firmware images.
- Firmwalker - is a script for searching the extracted firmware file system for goodies!
Setup or Overlay Unpackers / Extractors
- innounp - the Inno Setup Unpacker.
- Universal Extractor 2 (UniExtract2) - is a tool designed to extract files from any type of extractable file.
- lessmsi - a tool to view and extract the contents of an Windows Installer (.msi) file.
- FUU - [F]aster [U]niversal [U]npacker.
Binary PE Analysis / Editor (Windows)
- ProtectionID - Great little tool to scan a Windows binary payload for overlays and packers. File:ProtectionId.690.December.2017.zip VT link, pw: recessim.com
- RDG Packer Detector - is a detector for packers, cryptors, compilers, installers.
- PE-bear - is a Portable Executable reversing tool with a friendly GUI using the Capstone Engine and is Open Source!
- CFF Explorer - is a PE editor called CFF Explorer and a process viewer with a lot of features.
IAT Reconstructors (Windows)
- NtQuery Scylla - is a Windows Portable Executable imports reconstructor open source and part of x64dbg.
API monitoring ring3 (Windows)
- WinAPIOverride - is an advanced api monitoring software for 32 and 64 bits processes. You can monitor and/or override any function of a process.
- Rohitab API Monitor - is a free software that lets you monitor and control API calls made by applications and services. Its a powerful tool for seeing how applications and services work or for tracking down problems that you have in your own applications.
Debugger / disassembler for unmanged binaries
- Binary Ninja - reverse-engineering platform that can disassemble a binary and display the disassembly in linear or graph views.
- Ghidra - Ghidra is an open source software reverse engineering (SRE) framework developed by NSA's Research Directorate for NSA's cybersecurity mission.
- IDA - The IDA Disassembler and Debugger is an interactive, programmable, extensible, multi-processor disassembler hosted on Windows, Linux, or Mac OS X.
- Vivisect - Vivisect binary analysis framework. Includes Disassembler, Debugger, Emulation and Symbolik analysis engines. Includes built-in Server and Shared-Workspace functionality. Runs interactive or headless, programmable, extensible, multi-processor disassembler hosted on Windows, Linux, or Mac OS X (Pure-Python, using ctypes to access underlying OS debug mechanism). Supports RevSync via plugin, allowing basic collaboration with Binja, Ghidra, and IDA. Criticisms (from a core dev): "Graph View could use some work, slower than Binja and IDA (due to Python), documentation like an OpenSource Project... but we keep working to make it better. PR's and suggestions welcome." Best installed via Pip:
python3 -m pip install vivisect
- Veles - Open source tool for binary data analysis (No longer actively developed).
- Immunity Debugger - is a powerful new way to write exploits, analyze malware, and reverse engineer Windows binary files (python support)
- Hopper - Hopper can use LLDB or GDB, which lets you debug and analyze the binary in a dynamic way (only for Mac and Linux hosts, not for mobile devices).
- x64dbg - Is a powerful Open Source Ollydbg replacement with a User Interface very similar to Ollydbg also x64dbg as the name states offers x64 support.
- Reko - Reko is a binary decompiler for static analysis (ARM, x86-64, M68K, Aarch65, RISC-V and dotnet)
Debugging and Profiling dynamic analysis (Linux)
- valgrind - Valgrind is a GPL'd system for debugging and profiling Linux programs. With Valgrind's tool suite you can automatically detect many memory management and threading bugs, avoiding hours of frustrating bug-hunting, making your programs more stable.
- jTracer - is a stack trace visualization utility for libcsdbg. In other words, it acts as a TCP/IP server for libcsdbg clients, that connect to it and transfer their trace data, either C++ exception stack traces or generic thread stack traces and whole process stack dumps.
Debugger / disassembler for manged binaries
.NET
- dnSpy - is a debugger and .NET assembly editor. You can use it to edit and debug assemblies even if you don't have any source code available.
- ILSpy - NET Decompiler with support for PDB generation, ReadyToRun, Metadata (&more) - cross-platform!
- Telerik JustDecompile - is a free .NET decompiler and assembly browser that makes high-quality .NET decompilation easy With an open source decompilation engine.
- dotNET Tracer 2.0 by Kurapika - is a simple tool that has a similar functionality to RegMon or FileMon but it's designed to trace events in .NET assemblies in runtime. File:KDT2.0.zip VT1 VT2 (thermida packed), pw: recessim.com
.NET deobfuscators
- de4dot CEx - is a deobfuscator based on de4dot with full support for vanilla ConfuserEx.
- de4dot - is a .NET deobfuscator and unpacker.
JAVA
- Jadx - Dex to Java decompiler. Command-line and GUI tools for producing Java source code from Android Dex and apk files.
- Recaf - Recaf is an open-source Java bytecode editor that simplifies the process of editing compiled Java applications.
- JEB decompiler - Decompile and debug Android dalvik, Intel x86, ARM, MIPS, RISC-V, S7 PLC, Java, WebAssembly & Ethereum Decompilers.
- APKinspector - is a powerful GUI tool for analysts to analyze the Android applications.
- Apktool - A tool for reverse engineering Android apk files.
- Bytecode viewer - A Java 8+ Jar & Android APK Reverse Engineering Suite (Decompiler, Editor, Debugger & More)
Java deobfuscators
- deobfuscator - is a project that aims to deobfuscate most commercially-available obfuscators for Java. GUI version github
- Another Deobfuscator - Some deobfuscator for java. Supports superblaubeere27 / JObf / sb27, Paramorphism 2.1.2_9, Caesium, Monsey, Skid/qProtect, Scuti, CheatBreaker, Bozar, ...
PYTHON
- uncompyle6 - is a native Python cross-version decompiler and fragment decompiler. The successor to decompyle, uncompyle, and uncompyle2.
- pycdc - is a C++ python bytecode disassembler and decompiler.
PC platform exploration frameworks
- Chipsec - is a framework for analyzing the security of PC platforms including hardware, system firmware (BIOS/UEFI), and platform components. It includes a security test suite, tools for accessing various low level interfaces, and forensic capabilities.
- Metasploit Framework - is a Framework is a Ruby-based, modular penetration testing platform that enables you to write, test, and execute exploit code.
- Arachni - is a feature-full, modular, high-performance Ruby framework aimed towards helping penetration testers and administrators evaluate the security of web applications.
Mobile exploration frameworks
- Frida - Dynamic instrumentation toolkit for developers, reverse-engineers, and security researchers.
- objection - is a runtime mobile exploration toolkit, powered by Frida, built to help you assess the security posture of your mobile applications, without needing a jailbreak.
- AppAudit - is an efficient program analysis tool that detects data leaks in mobile applications. It can accurately find all leaks within seconds and ~200 MB memory.
- LSposed - is a Riru / Zygisk module trying to provide an ART hooking framework which delivers consistent APIs with the OG Xposed, leveraging LSPlant hooking framework.
- Xposed Framework - is a framework for mobile exploration hooking and modifying code on the fly. Inline API hooking example.
- Xposed modules
- JustTrustMe - Art framework hook to patch okHTTP and other common libs to fool the CERT chain in order for Mitmproxy to capture TLS traffic in cleartext.
- FakeXposed - Hide xposed, root, file redirection, two-way shielding data detection.
- Xposed modules
Promiscuous mode eavesdropping TCP/UDP
- mitmproxy - is an interactive TLS-capable intercepting HTTP proxy for penetration testers and software developers.
- wireshark - is a network traffic analyzer, or "sniffer", for Linux, macOS, *BSD and other Unix and Unix-like operating systems and for Windows.
- Mallet - is an intercepting proxy for arbitrary protocols.
Unified Extensible Firmware Interface (UEFI) & legacy PC BIOS Tools
- UEFI
- UEFITool / UEFIExtract / UEFIFind - is a UEFI firmware image viewer and editor.
- IFRExtractor-RS - is a Rust utility to extract UEFI IFR (Internal Form Representation) data found in a binary file into human-readable text.
- AMIBCP_5.01_x64 - is a tool from the manufacturer AMI (American Megatrends International) to modify the BIOS bin file with. VT link
- AMIBCP 5.01.0014 x64 VT link
- AMIBCP_5.02.0023 VT link
- AMIBCP_5.02.0031 VT link
- AMIBCP 5.02.0034VT link
- UEFI
- BIOS
- AMI
- AMIBCP_2.25 - AMI BIOS Configuration Program (AMIBCP) is a powerful customization utility that enables OEMs/ODMs to customize the Aptio® ROM image without intervening on the source code. VT link
- AMIBCP_2.43 VT link
- AMIBCP_3.13 VT link
- AMIBCP_3.37 VT link
- AMIBCP_3.46 VT link
- AMIBCP_3.47 VT link
- AMIBCP_3.51 VT link
- AMIBCP_4.53 VT link
- AMIBCP_4.55 VT link
- MMTOOL_2.22.1 - MMtool stands for Module Management Tool. As one of AMI's BIOS/UEFI utilities, MMTool allows users to manage firmware file modules within the Aptio ROM image. VT link
- MMTOOL_3.12 VT link
- MMTOOl_3.19 VT link
- MMTOOL_3.19_Mod_21FiX VT link
- MMTOOL_3.22 VT link
- MMTOOL_3.22_1B_21Fix-BKMOD VT link
- MMTOOL_3.22_CN_BKMod VT link
- MMTOOL_3.23_CN_BKMod VT link
- MMTOOL_3.26 VT link
- MMTOOL_4.50.0.23VT link
- MMTOOL_5.0.07 VT link
- MMTOOL_5.02.0024 VT link
- MMTOOL_5.02.0025 VT link
- Award
- Award Bios Editor - is a editor for Award bios.
- Insyde
- H2OEZE_x86_WIN_100.00.02.13 - H2OEZE™: Easy BIOS Editor that helps edit binaries in the BIOS, including Option ROMs, driver binaries, logos, and Setup values. VT link
- H2OEZE_x86_WIN_100.00.03.04 VT link
- H2OEZE_x64_WIN_100.00.03.04 VT link
- Download all tools in one archive, click here. [VT link]
Operating System for Penetration Testing & Digital Forensics
- Kali Linux - is an open-source, Debian-based Linux distribution geared towards various information security tasks, such as Penetration Testing, Security Research, Computer Forensics and Reverse Engineering.
- BlackBox is more than an operating system, it is a Free Open Source Community Project with the aim of promoting the culture of security in IT environment and give its contribution to make it better and safer.
- BlackArch - is an Arch Linux-based penetration testing distribution for penetration testers and security researchers.
- Parrot Security - is based on top of Debian, the most advanced and recognized universal operating system that can run anywhere.
- Fedora Security Spin - is a live media based on Fedora to provide a safe test environment for working on security auditing, forensics and penetration testing, coupled with all the Fedora Security features and tools.
- CAINE - CAINE (Computer Aided INvestigative Environment) is an Italian GNU/Linux live distribution created as a Digital Forensics project.
- Dracos Linux - is the Linux operating system from Indonesia, open source is built based on Debian live project under the protection of the GNU General Public License v3.0. This operating system is one variant of Linux distributions, which is used to perform security testing (penetration testing). Dracos linux in Arm by hundreds hydraulic pentest, forensics and reverse engineering.
- Pentoo - is a Live CD and Live USB designed for penetration testing and security assessment. Based off Gentoo Linux, Pentoo is provided both as 32 and 64 bit installable livecd.
Privacy Operating System
- Tails - is a portable operating system that protects against surveillance and censorship.
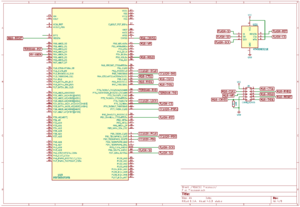
Tools for opening CAD or Boardview files
Description: Boardview is a type of file containing information about printed circuit boards, their components, used signals, test points and more. These files may have following extensions: .asc, .bdv, .brd, .bv, .cad, .cst, .gr, .f2b, .fz, .tvw and others.
- FlexBV - Advanced FlexBV boardview software integrates your boardview files with PDF schematics to substantially ease the process of tracking down faults and understanding damaged boards
- BoardViewer - BoardViewer is software intended for viewing various boardview file types
- CADview - simple old tool for viewing CAD files of PCB's. File:CAD View.zip VT link
For resources to open in your favorite boardview program visit Literature -> 1.2 Datasheets boardviews & schematics
Education
Tools are great, and sometimes free! Without knowing how to use them, they can be a big waste of time. Better to spend your time learning the basics, then apply your knowledge.
Reverse Engineering Tutorial - A comprehensive reverse engineering tutorial covering x86, x64, 32-bit ARM & 64-bit ARM architectures.