Difference between revisions of "Hardware Exploits"
Jump to navigation
Jump to search
(Created page with "thumb|Equipment typically used while exploiting hardware. Exploits in hardware typically used to extract firmware or gain debug access...") |
|||
| (5 intermediate revisions by one other user not shown) | |||
| Line 1: | Line 1: | ||
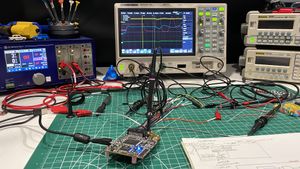
[[File:Lab Bench Hardware Exploit.jpg|thumb|Equipment typically used while exploiting hardware.]] | [[File:Lab Bench Hardware Exploit.jpg|thumb|Equipment typically used while exploiting hardware.]] | ||
| − | Exploits in hardware | + | Exploits in hardware used to extract firmware or gain debug access to locked microcontrollers. |
==Manufacturer Index== | ==Manufacturer Index== | ||
| + | [[Apex Microelectronics Exploits|Apex Microelectronics (APM)]]<br> | ||
| + | [[Atmel Exploits|Atmel (AT)]]<br> | ||
| + | [[China Key System Exploits|China Key System (CKS)]]<br> | ||
| + | [[GigaDevice Exploits|GigaDevice (GD)]]<br> | ||
| + | [[Microchip Exploits|Microchip]]<br> | ||
| + | [[STMicroelectronics Exploits|STMicroelectronics (STM)]]<br> | ||
| + | [[Renesas Exploits|Renesas]] | ||
Latest revision as of 19:42, 4 July 2025
Exploits in hardware used to extract firmware or gain debug access to locked microcontrollers.
Manufacturer Index
Apex Microelectronics (APM)
Atmel (AT)
China Key System (CKS)
GigaDevice (GD)
Microchip
STMicroelectronics (STM)
Renesas